In an effort to build and support a comprehensive and mature cybersecurity program, organizations have, through no fault of their own, unintentionally assembled dozens of point solutions over the last decade and beyond. While intentions were sound, logic was lost.
During this same stretch of time, astounding technological advancements have led to improved operational efficiencies, competitive differentiation, and convenience for both customers and employees alike. However, the speed of this innovation forced security minded executives to bless a ‘check box’ mentality for their security toolset, resulting in excessive expenses and clutter.
Leading an Economical and Efficient Infosec Program
Security leaders who are being asked to closely evaluate their spending without sacrificing risk levels should start by organizing their breach prevention arsenal into categories. Once identifying these categories and aligning them with larger business goals, look for solutions rather than ‘tools’ that can accomplish objectives in multiple areas, simplify your workflows, and allow you to cut unnecessary costs.
Let’s take a look at 8 key areas of cybersecurity programs where there are opportunities to be more economical and efficient while remaining vigilant and maintaining a strong security posture.
- Asset Inventory
- Vulnerability Assessment
- Threat & Vulnerability Management
- Network Detection & Response
- Threat Intelligence
- Security Information & Event Management
- Governance, Risk & Compliance
- Ticketing
Asset Inventory
Maintaining an up-to-date enterprise inventory system is very challenging. The set of assets in the enterprise changes constantly with devices being added and retired, physical machines migrating to virtual and various stakeholders constantly installing and updating software (with or without approval). Inaccurate inventory makes managing compliance and cyber-risk very difficult.
Balbix enables enterprises to maintain an accurate and up-to-date inventory of the organization’s assets. This includes all devices, apps, and services; managed and unmanaged infrastructure; on-prem and cloud; fixed and mobile; IoT, ICS, etc., and how they are used by your users. This inventory is available via real-time dashboards and search.

Vulnerability Assessment
While managing unpatched software is certainly a top-tier proactive measure, the collection and analysis of massive outputs require highly qualified security talent to engage in administrative tasks before any action can be taken. By the time the security team digests half of the report, the next scan has been completed and a new pile of vulnerabilities need to be addressed. Furthermore, traditional scanning solutions are unable to discern levels of mission criticality between assets.
Balbix analyzes your entire asset inventory continuously, in real-time and provides an active list of vulnerabilities, including and beyond CVE data taking into account issues like password reuse, misconfigurations, and unencrypted communications. Specialized AI categorizes and prioritizes security issues based on risk severity, taking into account breach likelihood and impact for each asset.
Threat & Vulnerability Management
Without vulnerability prioritization capabilities, it is difficult to know where to even begin with threat and vulnerability management. Prioritization allows you to base your patching activities on business risk and align your team’s efforts with overall business objectives. Proper prioritization often requires yet another solution beyond your scanning tool, resulting in an additional yearly expense and cumbersome workload for the team toggling between tools.
Balbix’s specialized algorithms analyze vulnerabilities based on severity, threat level, business criticality, exposure/usage, and compensating controls to prioritize security issues based on risk. Unlike legacy vulnerability assessment products, Balbix provides comprehensive vulnerability assessment across all asset types and 100+ attack vectors. Every risk insight is delivered with impact context and prescriptive fixes.
Network Detection & Response
Continuous monitoring of your network and a response plan are must-haves in today’s evolving threat environment. Reactive measures, unfortunately, have become a necessity based on the sheer volume of potential entry points. However, defaulting and over-reliance on reactive technology is a flawed approach. Organizations should shift their focus toward rock solid cyber hygiene and surfacing weaknesses across all assets, applications, and users prior to an event, these reactive measures become far more efficient and less resource intensive.
Balbix provides continuous visibility into all servers, workstations, laptops, mobile devices, and IOTs by monitoring real-time network traffic and gathering information from our host analyzers. Security issues being detected in real-time are delivered to the dashboard in a prioritized list based on risk level. Prescriptive fixes are detailed for every risk insight to ensure efficient remediation.
Threat Intelligence
In an effort for software companies to give customers maximum transparency, vulnerabilities are published by the thousands in the form of Common Vulnerabilities and Exposures (CVE). As the threat landscape evolves exponentially, teams are going as far as the darkest corners of the web to understand the subset of vulnerabilities that are being actively exploited by attackers. Because there are potentially thousands of sources of threat intelligence, it’s simply not a human scale problem to rank and prioritize the intel that helps uncover critical, exploitable vulnerabilities.
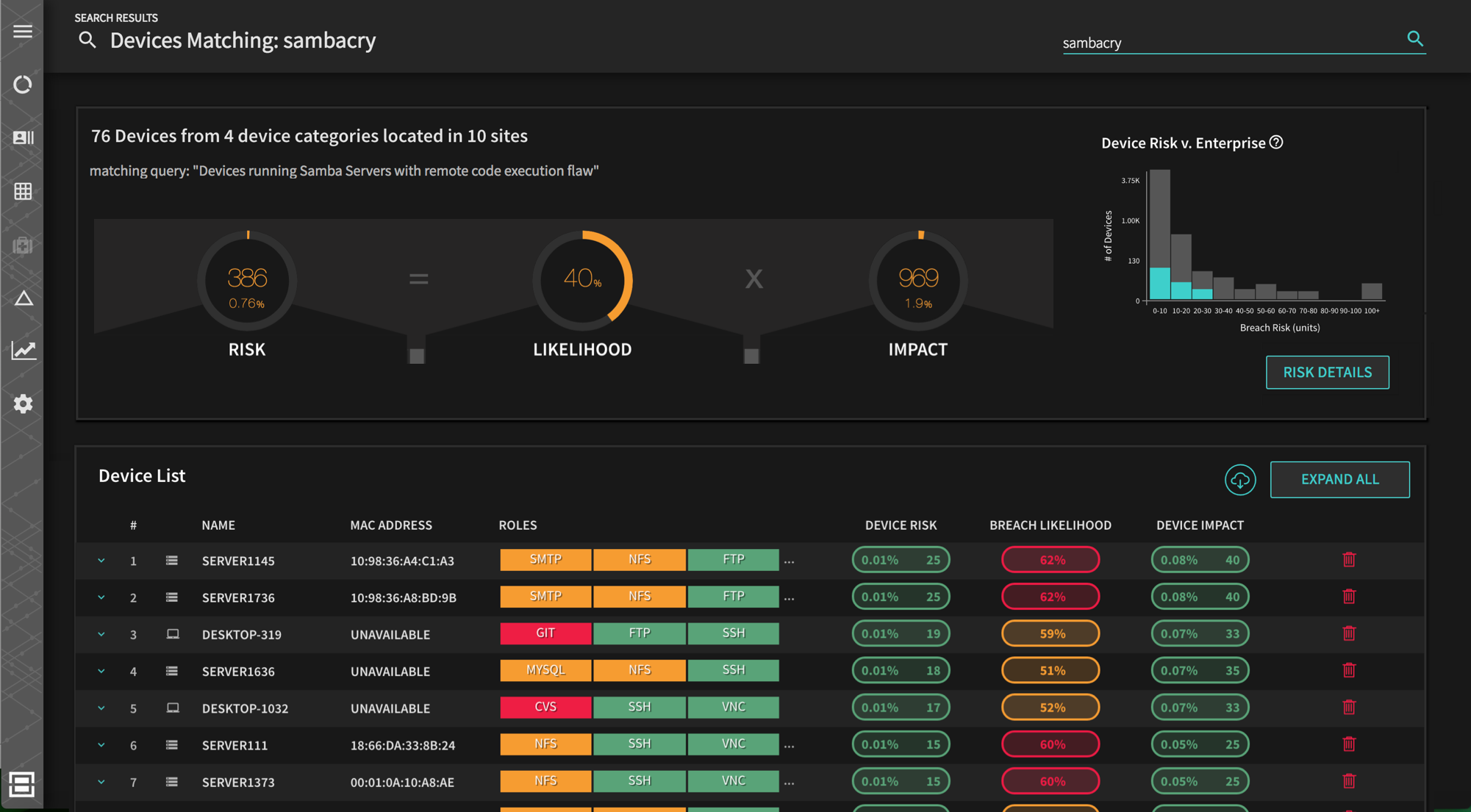
Balbix automates the ingestion of thousands of threat intelligence sources, comparing them to newly published CVEs and the assets within your organization to highlight the most relevant and critical risk insights for an organization. You can identify which assets are affected by specific threats using risk heat maps and google-like natural language search. Simply enter a query like “sambacry new york assets” and get risk insights for every asset (both managed and unmanaged) vulnerable to sambacry in New York. Balbix allows you to set up dynamic groups for risk areas of interest and monitor them continuously or assign them to other team members.
Security Information and Event Management
Similar to NDR, security information and event management has become a focal point for acting on security intel and making sense of overwhelming swaths of vulnerability data. SIEM tools typically pull data from other mitigating controls, network devices, servers, and domain controllers and aim to surface meaningful anomalies for necessary action. For that reason, it is not uncommon for an SIEM in a medium-size enterprise to produce 1,000s of security alerts each day.
Balbix allows SIEM solutions to serve their intended purpose as a backstop for identifying and actioning oversights. By automatically gathering threat intelligence from global threat feeds in addition to host and traffic analyzers deployed throughout an organization, Balbix provides a prioritized list of risk insights so that you can proactively fix security issues before they become mission critical.
Governance, Risk, & Compliance
Key to effective data governance and compliance management is an accurate and up-to-date inventory of all your enterprise’s data, categorized by departments and/or risk owners. Furthermore, you need to know which assets are holding highly sensitive information like customer PII or intellectual property. Mapping these items of risk toward an acceptable framework adopted by the business is how many decisions are being made. This means the accuracy of your data governance is driving the high-level understanding of risk and resource allocation.
Balbix allows you to simplify and accelerate regulatory compliance, providing real-time visibility into the security of all IT assets, apps, and users in your environment. This goes beyond standard GRC tools, monitoring the likelihood of compromise for each asset across 100+ attack vectors.
Ticketing (Security Orchestration)
Cyber risk insights are only valuable if they are both accurate and acted on appropriately with little delay. Too much time and energy is wasted debating what is and is not in need of attention without an agreeable source of truth in place. What security teams really need are clear risk insights delivered to specific owners with context and prioritized by severity. Proper security orchestration and ticketing should enable security teams to align their effort with results.
Balbix has direct integration with the most well used service desk solutions and generates prioritized tickets with relevant context assigned to the right owners for strategic and tactical mitigating actions. These tickets go beyond simple CVE numbers and detail prescriptive fixes for remediating each vulnerability. Notifications, leaderboards, and incentives can be set up for a gamified approach to drive cyber-risk reduction.
Doing More with Less in Cybersecurity
Even with heavy arsenals at their fingertips, security teams continue to struggle. Answering simple business questions posed by leadership continues to be met with overwhelmingly complex data and directionally ambiguous dialogue. If we stop, zoom out, and think pragmatically about what a security team is intended to do, the answer is fairly simple—enable business while reducing risk by understanding exposure. This should not require 50+ vendor subscriptions.
3rd generation cybersecurity posture platforms like Balbix enable security teams to bring all their risk mitigation programs together in one place. With one tool for continuous visibility into your attack surface and inventory, natural language search and heat maps, and prioritized actions items with prescriptive fixes, consolidating your tech stack and optimizing your infosec program might be easier than it seems.
