Now more than ever, it is critical that security leaders take measures to ensure cyber hygiene across their enterprise. Malicious actors are launching attacks against organizations of all sizes and their employees, who are by and large working remotely in the wake of COVID-19.
These cybercriminals have shown that they have no ethical boundaries. On March 11, Champaign-Urbana’s Health District was held hostage by a ransomware attack. 4 days later, the US Health and Human Services Department was hit by a DDos attack. Most repulsive perhaps was the attack against the World Health Organization, where criminals set up a website imitating the WHO’s internal email system to steal login credentials from the organization’s employees.
For ordinary companies, risk levels are spiking at frightening levels as the extended perimeter becomes more and more difficult to control. Phishing emails and malicious websites have increased dramatically in the last month as hackers try to exploit coronavirus-related keywords. Between March 9 and 23, a whopping 317,000 new phishing websites were created.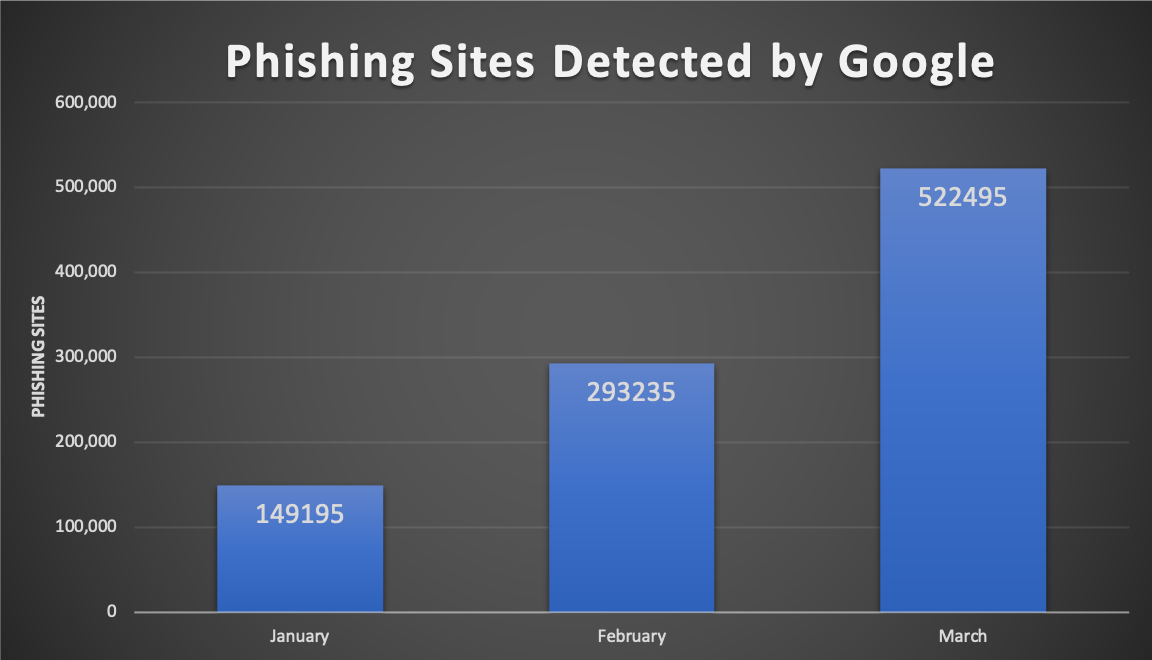
Security teams have their work cut out for them, but should not let a sense of dread demotivate them from securing what they can control. Data breaches happen in stages and typically over lengthy periods of time, with numerous steps needed to exfiltrate sensitive data. Key to stopping the oncoming attacks in their tracks is implementing strong cyber hygiene measures across the organization.
Here are 11 steps that CISOs can take to improve cyber hygiene and protect their enterprise.
1. Keep a real-time inventory of all hardware and software on the company network
Maintaining an up-to-date enterprise inventory system is very challenging. The set of assets in the enterprise changes constantly with devices being added and retired, physical machines migrating to virtual and various stakeholders constantly installing and updating software (with or without approval). Since you can’t improve what you can’t measure, inaccurate inventory makes managing compliance and cyber-risk impossible.
2. Make VPN accessible for all employees
Companies with large remote workforces typically have a robust VPN solution available to their employees. But for organizations who aren’t used to employees working from home, mobilizing to VPN can be a nightmare at first. Unfortunately, it’s a must-have for employees accessing the corporate network and private resources.
Prioritize access for your senior staff and privileged users first since their assets being compromised would have a much greater impact on the business. Once you’ve deployed across the company, ensure you have visibility into all VPN connections.
3. Get comprehensive visibility into your extended perimeter (port exposure, security configuration issues, missing or default passwords, broken certificates, etc.)
A breach usually begins with one or a handful of vulnerable systems on the extended perimeter being compromised. This might happen because of an employee being phished, or via a weak password, or some unpatched vulnerability. In rare cases, the adversary may use a zero-day exploit to establish this initial beachhead. With remote work on the rise, your extended perimeter is more vulnerable than ever before.
4. Monitor password strength and re-use among employees
In almost all organizations, there are numerous instances of weak, default and reused passwords, often stored and/or transferred in the clear. Some CISOs and CIOs try to address this problem with strong password policies, which lead to much angst amongst users who are forced to somehow remember dozens of nonsensical strings.
Even such policies can’t address the more problematic issue of password reuse, which frequently extends to platforms and accounts beyond the security team’s control. Then, there are password issues related to poorly designed software which stores or transmits passwords in the clear or improperly encrypted. One might even say that passwords have their own secret lives.
5. Roll out controls for endpoint protection among all employees
As I mentioned earlier, the number of malicious websites and phishing scams are skyrocketing in the midst of the Covid-19 pandemic. Get ahead of your employees falling victim to these scams by rolling out strong controls for endpoint protection for all employees. The endpoint protection you roll out for each department or division should depend on the business criticality of that team’s assets. If you’ve already implemented strong endpoint protection, make sure to validate that endpoint visibility remains consistent for users that are now remote.
6. Prioritize patching for business critical assets
In most organizations, when an urgent and/or high severity vulnerability needs to be addressed, all assets tend to be treated with equal, high priority. As new vulnerabilities arise with the shift to working from home, it is important that business critical ones are addressed first. For instance, patching the CFO’s laptop is much more important than patching your office coordinator’s laptop.
7. Audit the number of users with admin privileges on business critical applications
The more users you have with admin privileges on business applications, the higher likelihood there is that those assets can be exploited. If admin credentials on a critical asset were to be compromised, it could be the gateway to a major breach. To combat this, identify your most business critical applications and audit the number of users with admin privileges.
8. Identify at-risk users and risk owners and implement training measures
Monitoring web traffic and hygiene among your users is critical to predicting breaches. Once identified, high-risk users can be given training or subjected to tighter endpoint controls. Owners of risk, like a Director of Customer Satisfaction who is responsible for customer PII, should also be identified and educated on security measures they need to take.
9. Establish strong user identity via multi factor authentication
The ability to identify users who are trying to access some enterprise resource or application in a robust manner is extremely important. Practical strong user identity can be established using an enterprise Identity and Access Management (IAM) product like Okta, combined with a password manager like 1password. This will give you robust multi-factor authentication and policy control where possible and enable good password hygiene across managed and unmanaged applications.
10. Establish strong device identity and application identity capabilities
Strong device identity can be established using client-side certificates and strong application identity can be established using server-side certificates. Mechanisms must be put into place to refresh expiring certificates and identify and educate users who click past certificate warnings.
11. Closely track assets that would have severe impact if breached
We touched earlier upon the importance of prioritizing your business critical assets when patching. Building on this, it is extremely important to maintain continuous visibility of these assets and track them closely so that you are aware of vulnerabilities affecting these assets as they arise.
Sanitizing your attack surface with Balbix
Balbix continuously observes your extended enterprise network inside-out and outside-in, to discover the attack surface and analyze hundreds of millions (or more) of data points that impact your risk. You can automatically discover, analyze, and categorize all devices, apps, and services including managed and unmanaged, infrastructure, on-premises and cloud, fixed and mobile, IoT, ICS, etc.
Balbix also provides a real-time, prioritized list of action items that will affirmably reduce risk. To learn more about Balbix, request a demo here.

