August 25, 2023
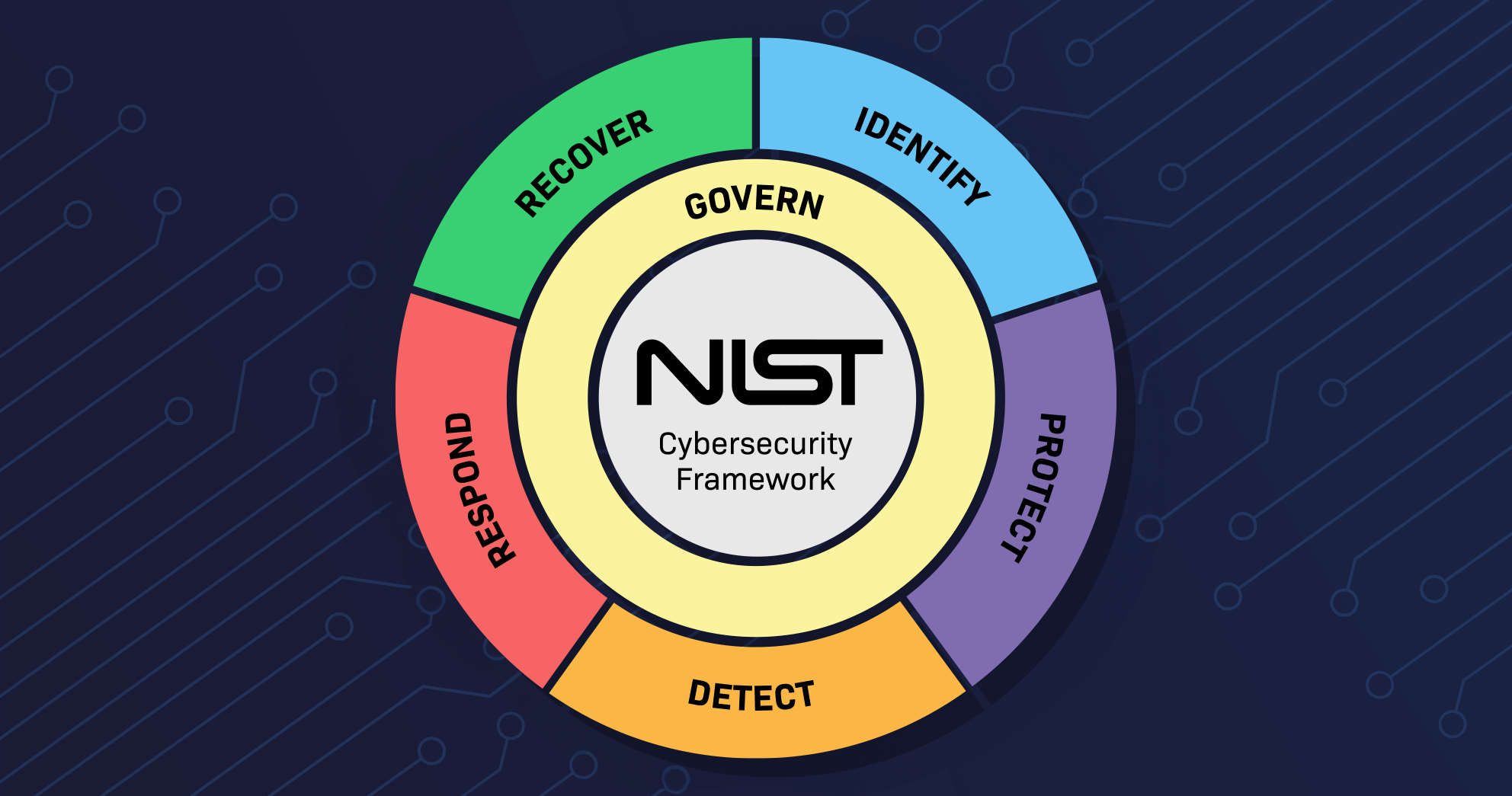
NIST CSF 1.1 to 2.0 is a significant update reflecting an inclusive and responsive approach to risk management. The most recent public draft of NIST CSF 2.0 includes expanded guidance and adds a sixth function, ‘Govern,’ to aid organizations in reducing cybersecurity risk. The NIST CSF 2.0 public draft aligns with feedback from Fortune 500 customers, and we encourage organizations to incorporate these new guidelines.
While NIST is accepting public comment on the draft framework until Nov. 4, 2023,it does not plan to release another draft. The developers plan to publish the final version of CSF 2.0 in early 2024.
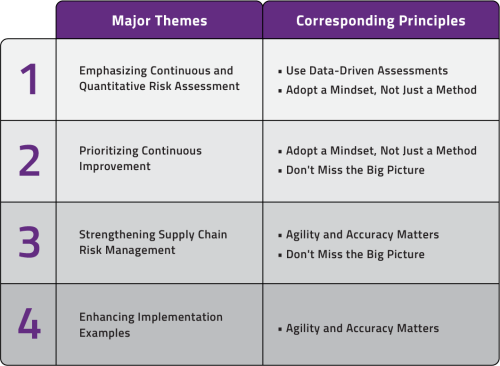
Let’s look at each of the recommendation themes in a bit of detail:
Continuous risk assessments are essential for an effective security program, underpinning the improvement of risk posture and advancement to higher implementation tiers. Recognizing the importance of a consistent understanding of critical IT assets, threats, security weaknesses, and the likelihood of exploitation, Balbix recommended the inclusion of continuous risk assessments in NIST CSF 2.0.
At a broad level, this recommendation is covered by introducing the Govern function (GOVERN (GV): Establish and monitor the organization’s cybersecurity risk management strategy, expectations, and policy). At a specific level, it materialized in sub-categories such as “GV.RM-06: A standardized method for calculating, documenting, categorizing, and prioritizing cybersecurity risks is established and communicated,” with implementation examples like “Establish criteria for using a quantitative approach to cybersecurity risk analysis, and specify probability and exposure formulas.” The new draft further refines the understanding of cybersecurity measurement with updates and new pointers to NIST SP 800-55. This focus on continuous assessment is crucial in today’s dynamic threat landscape.
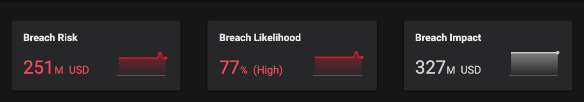
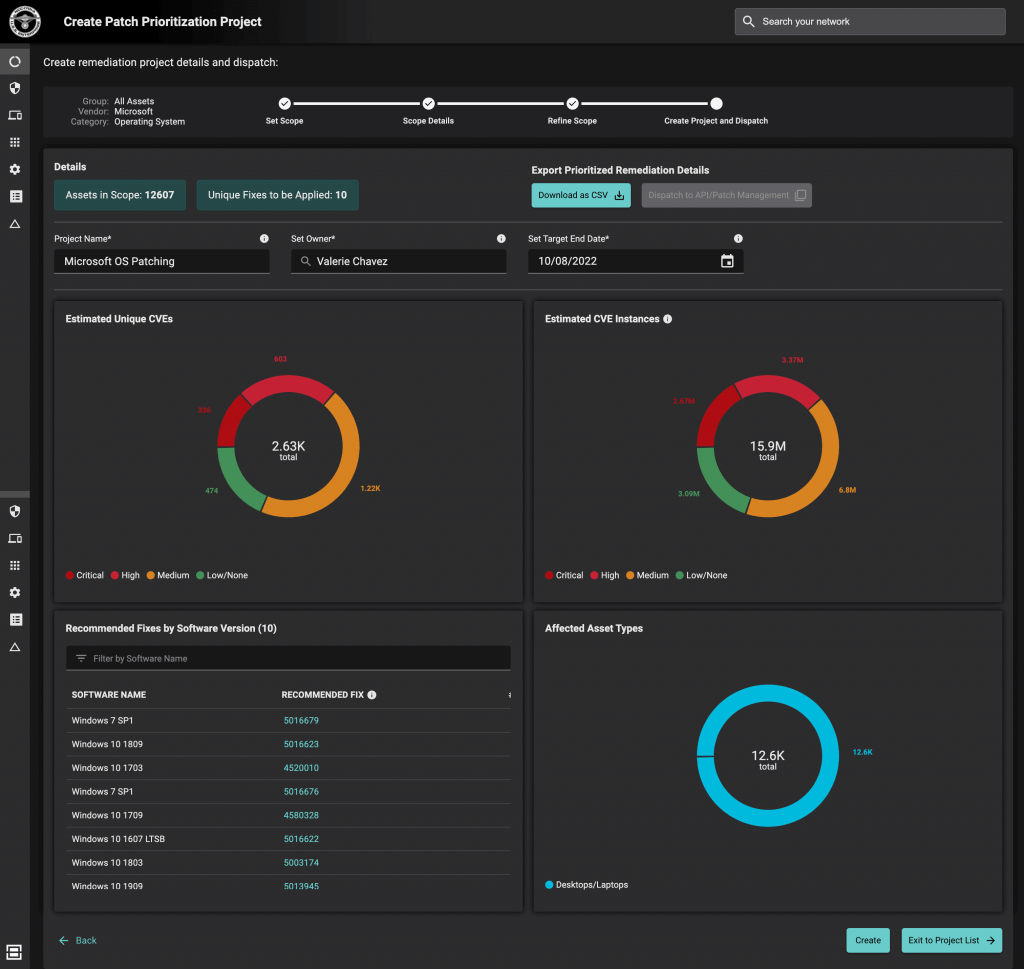
Balbix achieves more precise and accurate risk quantification with a data-driven approach. It ingests data from dozens of security, business, and IT tools categories like IT Asset Management, Cloud, CMDB, EDR/XDR, Vulnerability Assessment, IoT/OT, CSPM, BAS, Networking, and more to build a unified inventory of assets. It collects data about assets (laptops, mobile, IoT/OT, cloud services), applications, and their associated vulnerabilities to estimate breach likelihood and impact in granular detail. Balbix’s impact model includes automated asset criticality analysis, breach loss model based on analysis of many thousands of actual breaches, and minimal customer input to minimize the risk of subjective guesswork. The risk quantification can be traced to granular views, such as per asset or vulnerability view.
Continuous improvement is more than a mere concept; it’s a vital journey that organizations must embark on. This approach is crucial in cybersecurity, a rapidly evolving field where threats and challenges constantly emerge. For example, software patched and secured yesterday might be vulnerable to today’s newly discovered exploit, making constant adaptation and improvement essential. This mindset emphasizes that cybersecurity isn’t simply about implementing the next incremental category or subcategory of the NIST CSF; it’s about adopting a dynamic and holistic stance. We’ve seen from enterprise organizations that those who truly commit to risk reduction and continual improvement have much more success in reducing cyber risk in practice. Those who don’t typically struggle to handle/reduce their risk.
The NIST CSF 2.0 draft embraced this perspective by introducing a new Improvement Category in the Identify Function’s ID.IM section (Improvements to organizational cybersecurity risk management processes, procedures, and activities are identified across all Framework Functions). The draft also updated the implementation tiers definition and now includes factors like cybersecurity risk governance, cybersecurity risk management, and third-party cybersecurity risks, underscoring a shift to a more holistic approach.
Balbix provides insights and specific actionability to enable organizations to improve their key metrics continually. Some examples-
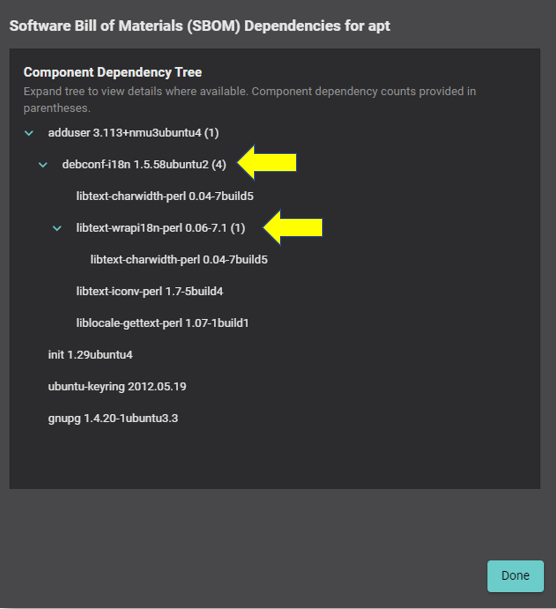
Recent attacks such as Log4j, SolarWinds, and Spring4Shell have heightened concerns about software supply chain vulnerabilities. Most organizations struggle to produce a software bill of materials (SBOM) for their in-use applications, highlighting a significant gap in this area. We recommended that the NIST CSF framework emphasize the inclusion of the SBOM.
The NIST CSF 2.0 draft places Supply Chain Risk Management under the Govern function. In this section, Cybersecurity Supply Chain Risk Management (GV.SC) is addressed, stating: “Cyber supply chain risk management processes are identified, established, managed, monitored, and improved by organizational stakeholders.” Furthermore, GV.SC-05 delves into the details with an implementation example: “Contractually require suppliers to provide and maintain a current component inventory (e.g., software or hardware bill of materials) for critical products.”
Balbix offers near-real-time visibility into your entire IT environment, providing a comprehensive asset inventory and a detailed runtime SBOM view. This lets you identify all software components deployed in your environment, including their versions, install path, and full dependency path. Balbix infers vulnerabilities associated with the software and related components, enabling security teams to respond to the next log4j-style vulnerability much faster.
Balbix recommended adding implementation examples to the NIST Cybersecurity Framework (CSF) to render it more operational and accessible. By incorporating these examples into the core of the CSF, the intention is to enhance its practical application and streamline use, thereby encouraging best practices within the field.
The latest NIST CSF 2.0 draft includes implementation examples for Subcategories and provides more framework mapping resources. These updates make the framework more user-friendly and adaptable to various organizational needs, reflecting a real-world approach. Including specific implementation examples directly supports organizations by offering concrete, actionable guidance. It allows them to better understand and apply the framework’s principles in their unique contexts. The changes in NIST CSF 2.0 underscore the importance of clear and specific guidance, aligning closely with Balbix’s recommendations for a more functional and responsive approach to cybersecurity management.
It is encouraging to see the incorporation of some of our insights in the updated NIST CSF 2.0 draft. These changes, including the introduction of the new ‘Govern’ function, the addition of practical implementation examples, and an increased focus on continuous improvement, would substantially enhance the effectiveness of cybersecurity practices across various organizations. Together, these improvements solidify the NIST CSF’s position as a vital tool in shaping cybersecurity strategy and risk management. Balbix is proud to contribute to this evolution, ensuring that the framework remains adaptable and aligned with the dynamic nature of today’s cybersecurity landscape.