November 18, 2022
CRQ (Cyber Risk Quantification) is the latest acronym doing the rounds in the cyber security industry. Many security professionals regularly use this acronym but few actually understand what CRQ is and even fewer know how to implement it.
In this blog, I will attempt to demystify the concept of CRQ, express why a robust CRQ model is an essential requirement for every organization and describe the compelling business value it offers to those who have successfully implemented it. Finally, I will discuss the two primary approaches currently advocated in the market, highlight a few limitations of these approaches and provide details of a more effective way to implement CRQ.
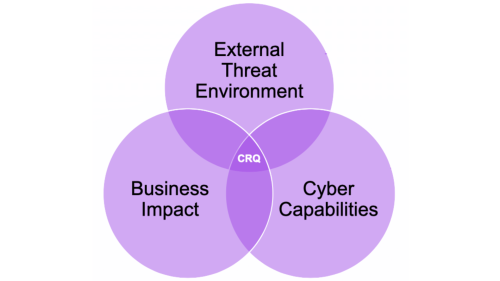
Simply put, CRQ is the quantification of an organization’s cyber risk expressed in monetary terms. An organization’s cyber risk is the intersection of its internal and external threat environment, its current cyber capabilities (i.e. security controls and other mitigations that exist within the organization), and the business value at risk from a cyber attack. CRQ enables an organization to express this interaction in a language that is understood and accepted by a large number of internal and external stakeholders.
CRQ is a key enabler for risk-based business decision making. It allows CISOs and their infosec teams to articulate cyber risk to senior management and the Board in a language that is consistent with the way other risks such as market, credit and operational risks are presented. Its ability to do so is extremely powerful. In my previous role, I witnessed the stunned reaction of a non-executive director when he realized that their cyber exposure was in the hundreds of millions of dollars! What ensued was a flurry of requests to understand the drivers of this risk and the actions that the organization could take to mitigate it. More generally speaking, CRQ empowers the CISO to:

So how does an organization actually implement CRQ? Two schools of thought have emerged over the last few years. These are the Top Down and Bottom Up approaches to CRQ. By far, the more popular choice is the Top Down approach which utilizes scenarios and high level assumptions to estimate risk in monetary terms. This calculation is usually performed at the enterprise level. Based on my experience working with many clients, this approach has the following limitations:
The other side of the coin is the Bottom Up approach to CRQ. This involves an asset by asset risk assessment. This is an approach that is attempted by customers who are at the more sophisticated end of the cyber risk management spectrum and usually involves creating a DIY data lake to feed the risk model. Needless to say, this is an incredibly challenging problem to solve. A few implementation pitfalls that need to be navigated include:
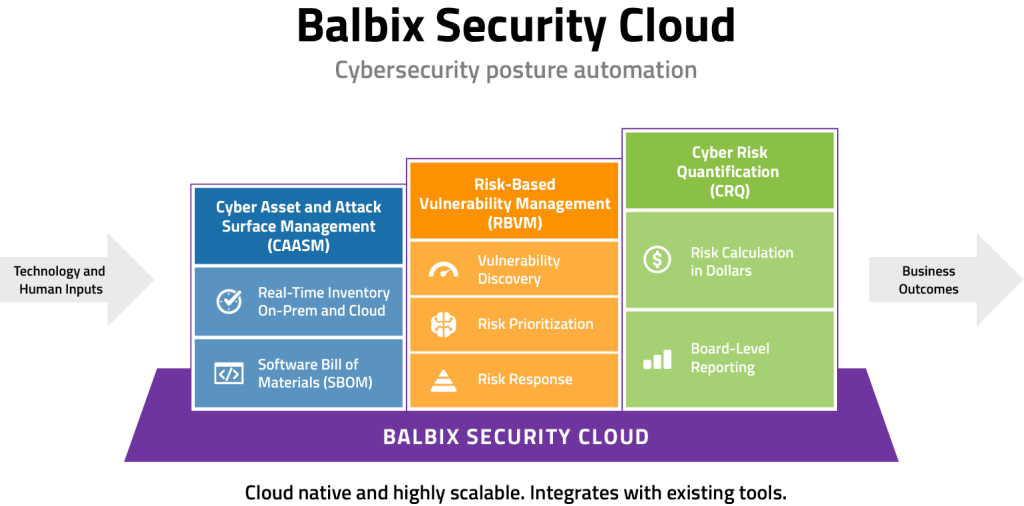
So here we are today and I ask myself if there is a better approach to CRQ that leverages the strengths of both the Top Down and Bottom Up approaches whilst negating their limitations. The answer is an emphatic YES. We at Balbix have developed an AI-powered, market-leading, dynamic CRQ model that estimates your enterprise breach risk in real time and surfaces key risk issues along with prioritized mitigation recommendations. So how do we do it?
Our SaaS platform, the Balbix Security Cloud, is the only solution that:
If you would like to learn more about the Balbix CRQ model and methodology and the benefits it brings to your cybersecurity posture management, please do get in touch.