December 8, 2022
As 2021 turned to 2022, the internet was on fire. Organizations around the world began identifying and remediating recently discovered Log4j vulnerabilities. Many of our customers, including a Fortune 100 company, contacted us for urgent assistance. Fortunately, we were in a position to help. We had the ability to produce a software bill of materials (SBOM) on demand for these application packages and applications. We continued to help as additional critical software component vulnerabilities were identified (think Spring4Shell and OpenSSL).
Today I’m excited to announce that we can now provide organizations with a comprehensive inventory of the SBOM of their software products. This includes an accurate multi-level dependency mapping, an industry first. By using the SBOM, our customers can identify and remediate software component vulnerabilities at unparalleled speed and scale. They can do so irrespective of whether their assets are on-premises or in the cloud. We now also allow them to export their SBOM inventory data in industry-standard formats to enrich their CMDB and inform other tools and workflows.
Before I go into greater detail about our announcement, let me back up a bit.
According to the Cybersecurity Infrastructure and Security Agency (CISA)’s definition, “a SBOM is a nested inventory, a list of ingredients that make up software components”. The SBOM has emerged as a key building block in software security and software supply chain risk management.
The importance of maintaining a SBOM gained momentum after the May 2021 U.S.Executive Order 14028, which included specific directives related to SBOM. The order requires software vendors to provide a SBOM for their software products. In response to the order, the National Telecommunications and Information Administration (NTIA) have defined the minimum elements for a SBOM including the details and supply chain relationships of various components used in building software.
An SBOM helps security teams improve their visibility. One of the customers who we worked with closely on Log4j remediation shared an analogy. The analogy is of a fishing boat on the water. On the boat, they have many tools that can tell them what is on the surface of the water, they said. But they don’t have any tools to see below the surface. Similarly, they can see their assets but they can’t see the SBOM of the software products on those assets. They felt that having the SBOM from Balbix was like being able to identify every fish, and even every octopus, all the way to the bottom.
The Log4j vulnerabilities were widely regarded as one of the most complex and serious security flaws. Unfortunately, software component vulnerabilities like these have been on the rise in the last few years. This is due in no small part to the ubiquity of open source software. The 2022 Open Source Security and Risk Analysis Report notes that open source software vulnerabilities pose significant exposure to the software supply chain: “of the 2,409 codebases analyzed by Black Duck Audit Services for this year’s report, 97% contained open source. Eighty-one percent contained at least one known open source vulnerability.”
If you work at a large organization, for example the Fortune 100 company I mentioned above, 10,000s of your assets could be impacted by a new software component vulnerability. Finding occurrences can be complex since software components can be used by applications in many ways. They can exist as a standalone application, as a library resource, as part of an archive file, or be embedded in a custom application.
Static analysis tools can provide a view of the SBOM dependencies for home grown applications. But, that is not true when it comes to obtaining a SBOM for the third party applications that use many open source and commercial libraries. Log4j was a classic example where literally anyone producing a java application was using this library.
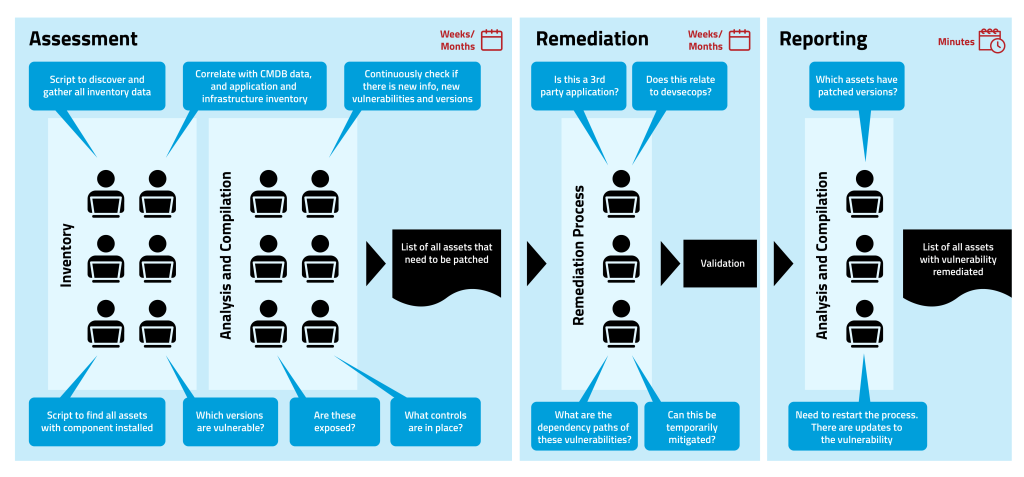
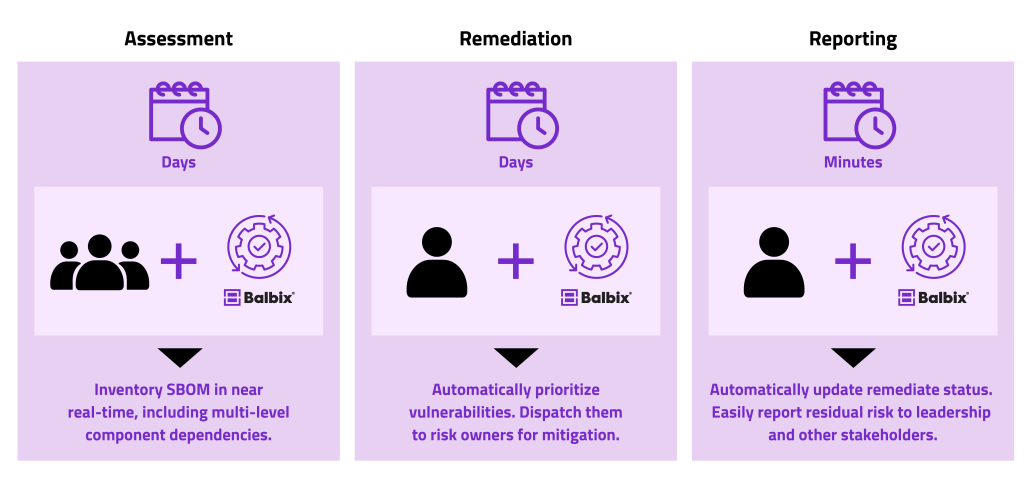
Without an accurate SBOM, identifying the instances where this vulnerability exists may take weeks, and probably months. It certainly took that long for many companies to discover all their instances of Log4j. The discovery phase involves a complex workflow dealing with CXOs, IT and network security teams, vulnerability management teams, application security teams, incident response teams, while keeping updated on the latest vendor and industry guidance. Responding and reporting on status could also take additional weeks of time.
There is now a way to put this pain behind you. With our announcement today you can now use Balbix to:
You can’t protect what you don’t know. Balbix provides near real-time inventory of the SBOM at scale. You can now know exactly which software components (and versions) are deployed in your environment. That includes the full dependency path, version of the components and open source and third-party packages. To perform a complete dependency analysis of all installed software, Balbix Host Analyzer uses package managers and live process analysis at run-time. We provide this inventory whether assets are located on premises or in the cloud. For the initial release, Balbix is surfacing the SBOM details provided by the most popular package managers across the various software distributions. We will continue to expand coverage going forward.
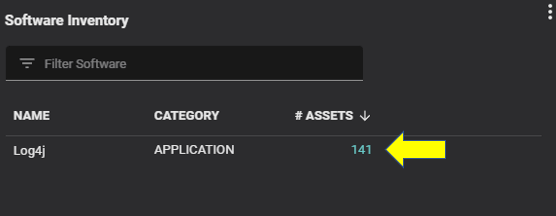
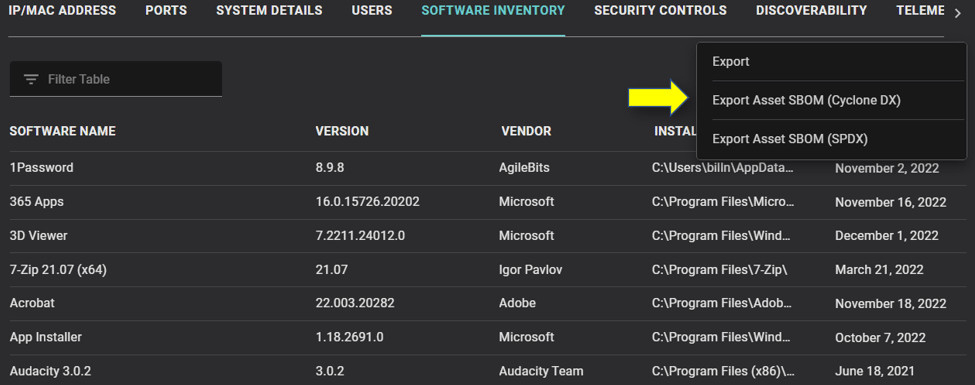
For each asset, Balbix compiles a software inventory (as seen below) and then provides an SBOM for each software product.
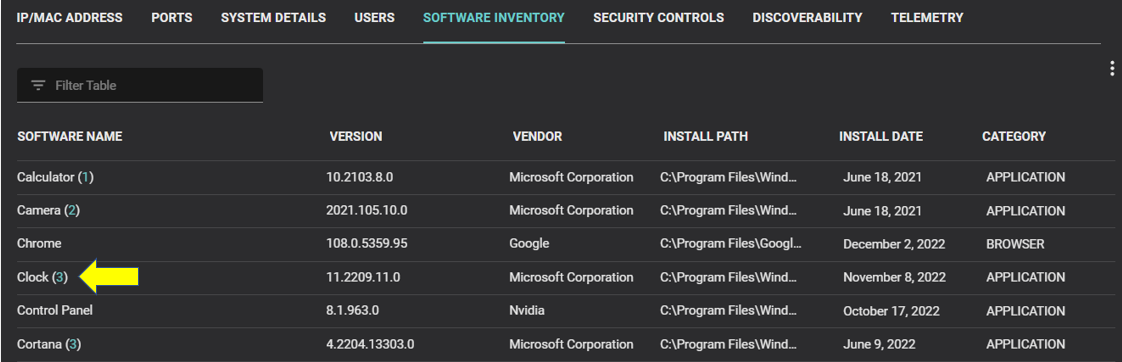
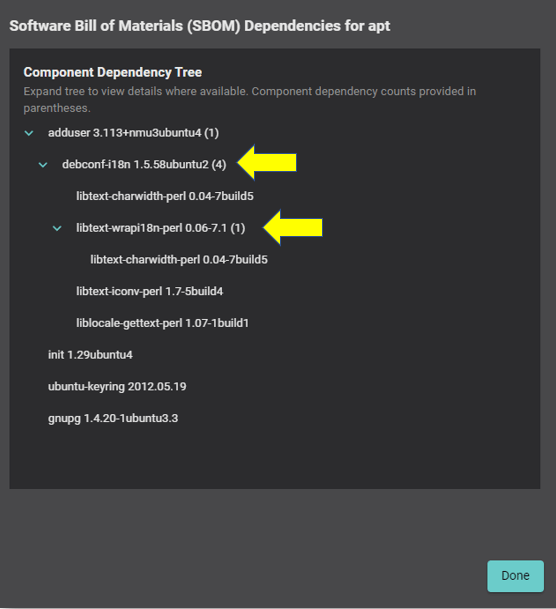
For the SBOM, Balbix doesn’t merely provide a list of components. Rather, we provide a complete mapping of software component dependencies, including multi-level and nested dependencies.
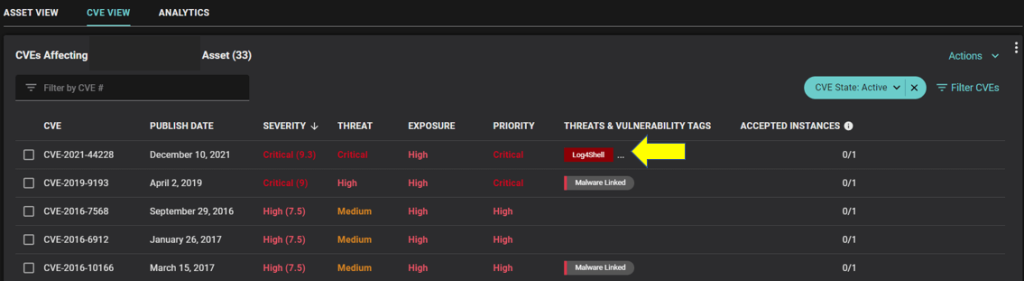
Having near real time visibility of your SBOM is half the battle. It was critically important to enable visibility into complex vulnerabilities such as Log4j and Spring4Shell. The other half of the battle is being able to identify, prioritize and remediate assets with software component vulnerabilities. Balbix helps you with this too.
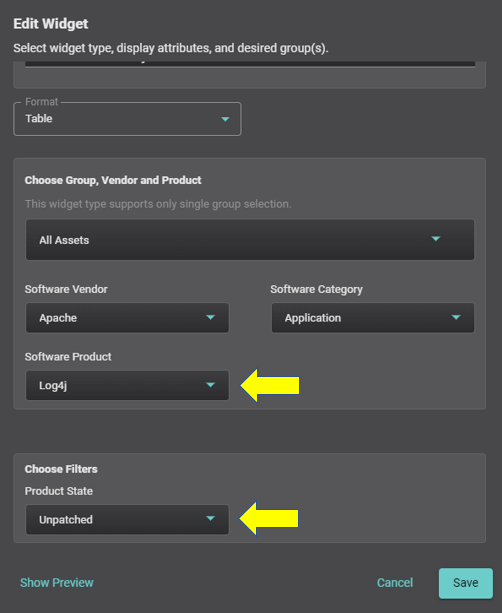
To identify software component vulnerabilities using Balbix, you simply search the assets in your environment for unpatched or vulnerable software. The example below shows a search for assets with unpatched Log4j software components, and the resulting search results.
Balbix identifies vulnerable assets by combining information from the SBOM inventory with common vulnerability and exposure (CVE) data and service information (ports, services, related environment variables, etc.) to infer software component vulnerabilities and their usage and exposure. Vulnerabilities are identified with accuracy (i.e. few false positives) at unparalleled speed and scale. Vulnerabilities are also prioritized based on their risk to your organization. You can then notify risk owners to remediate them using suggested fixes and automatically receive updates when the patches have been applied.
The automation of software component vulnerability management saves you time and effort. As the Fortune 100 company mentioned above later noted, “accuracy, specificity and actionability have been the key factors in tracking this vulnerability and remediations/mitigations. With Balbix’s help, [we] reduced the end-to-end risk mitigation workflow time from months to weeks.”
Software component vulnerability management can also be delegated to less experienced staff since much of the vulnerability discovery and remediation tracking is done through automation. Experienced resources no longer need to write scripts to identify vulnerability instances and their execution paths, and can work on more strategic initiatives.
Unlike other cyber asset attack surface management (CAASM) solution providers, Balbix allows security teams to export their SBOM inventories in industry-standard formats. We currently support two formats: Open Web Application Security Project (OWASP), Cyclone DX, and Software Package Data Exchange (SPDX). IT and security teams can export their SBOM inventory to popular configuration management database (CMDB) tools.
I am very excited about the new functionality enabled by our new SBOM capabilities. The next time there is a critical software component vulnerability, the internet won’t be “on fire” to the same degree.