December 2, 2022
Having a broad range of security tools is necessary to ensure a strong security posture. Any good security strategy will have a diverse set of tools providing a defense in depth and breadth in order to keep sensitive data safe and enable operations to run smoothly. Unfortunately, the data produced by these tools is almost always kept siloed within the tool and analyzed independently.
This is problematic. It can lead to a lack of communication between tools, and an inability to aggregate and search the data. For example, your vulnerability scanners likely don’t take into account the data that your endpoint management tool sees, and vice-versa. It can also lead to decisions being made in an incoherent manner.
To overcome this, security teams engage in manual analysis to produce a unified asset inventory with appropriate attributes and vulnerabilities mapped to those assets. This can be laborious as security teams have to log in to multiple platforms to get the information they need about their assets. More fundamentally, it isn’t a process that can scale to match the volume of security data being produced today.
This is also when the system begins to break down. With manual analysis comes the danger of mistakes, which can lead to assets and their vulnerabilities being incorrectly classified. Worse, assets and issues can be missed altogether.
The purpose of this blog is to provide some guidance on how to overcome these challenges and discuss how Balbix can help you ensure your asset coverage and visibility is accurate and complete. This blog builds on my previous blog where I outlined how Balbix builds an accurate view of assets and tracks the deployment of security controls.
Cyber asset attack surface management (CAASM) is an emerging technology area focused on enabling security teams to overcome asset visibility and exposure challenges. Data is gathered primarily through API integrations with existing tools. It enables organizations to have a unified inventory of all of their assets (internal and external) and their software products (including versions and software components). A CAASM solution should also allow security teams to query the consolidated data, identify the scope of vulnerabilities and gaps in security controls, and remediate issues.
Balbix’s CAASM solution provides the capability to continuously ingest data from your cybersecurity and IT tools. During this process, all data is aggregated, deduplicated, and correlated to give you a unified view of your environment. Security and compliance teams can then easily search and manage the entire inventory of assets and create custom views for tracking metrics and identifying, prioritizing and remediating issues.
Below, I cover how Balbix helps with four CAASM use cases in greater detail:
You can read about other use cases, including Balbix’s software bill of materials (SBOM) capabilities and how a Fortune 100 used Balbix to discover and remediate log4j vulnerabilities, elsewhere on our website.
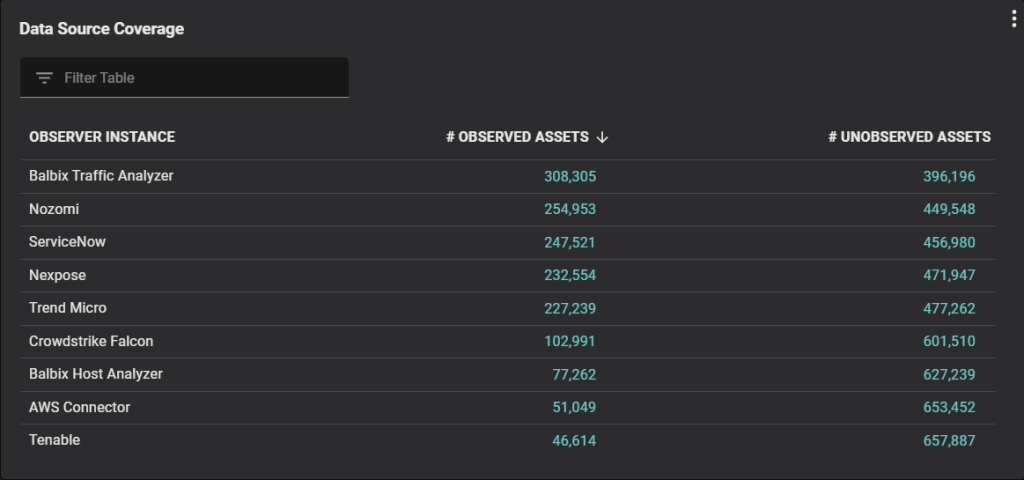
One of the top benefits of having an asset inventory is being able to monitor your security control coverage. As you can see in the chart below, Balbix provides a view on how much coverage all of your tools have including, but not limited to, security controls. The numbers of observed and unobserved assets are clickable and allow the user to drill down into a full asset list. This makes gaps in coverage easy to identify.
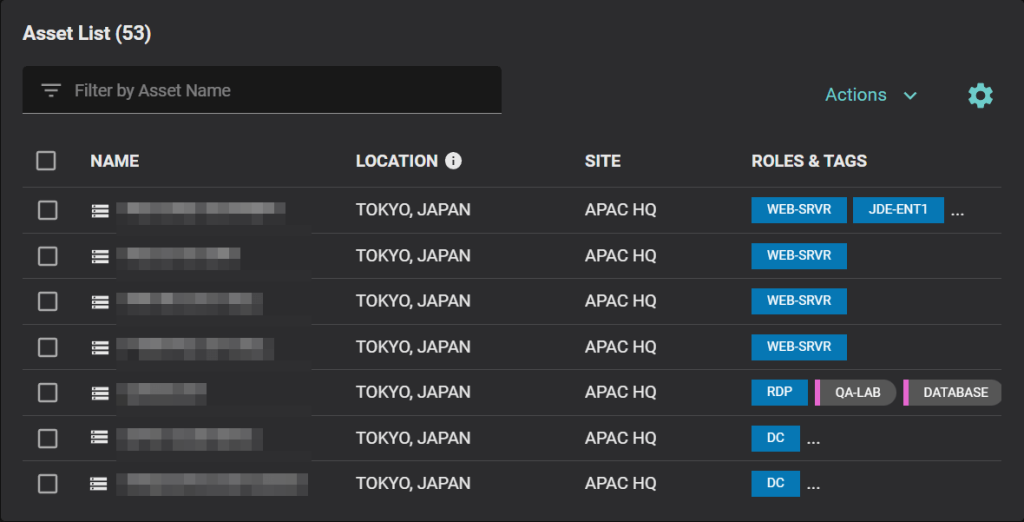
An example of putting a project into action would be an IT admin who manages the Tokyo office and wants to make sure her security tool deployments are complete for Windows servers under her purview. In Balbix, she can easily isolate Windows servers in any given geography (or site) and see where any gaps may lie. Below you can see that the vulnerability scanner, in this case Nexpose, is actively scanning 73 servers but missing 8 servers, and Crowdstrike Falcon is only deployed on 28 systems but missing on 53 systems.
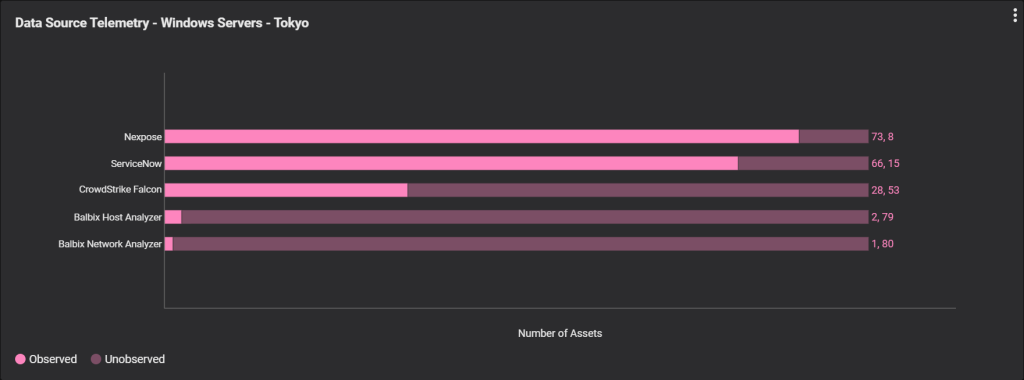
To identify the systems where there are gaps in coverage, and to begin resolving the issue, all you would need to do is click into the missing systems portion of the bar chart to see a complete list of servers that need attention (see below). Technicians can work directly from this list, or export the list as a CSV file if a downstream ticketing system needs to be used.
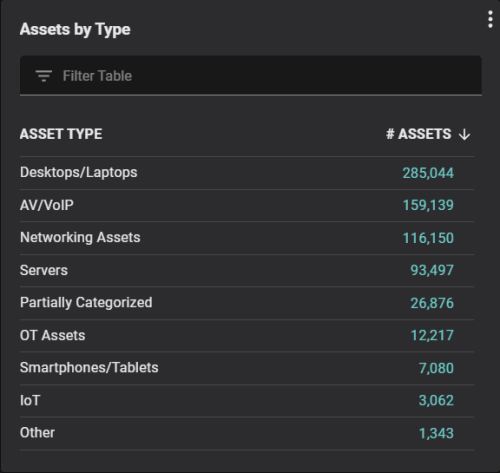
In addition to providing coverage for security tools, Balbix also provides a breakdown of the types of assets that are present to give managers and technicians insight into your overall landscape and a better understanding of your network architecture. Balbix does this categorization automatically and does not have to rely on external data sources like a CMDB to do so. This ensures that data is continuously updated instead of coming from stale or outdated classifications captured elsewhere.
Balbix can provide a breakdown across your entire enterprise or individual segments (for example your Tokyo office). You can also drill in and inspect all assets within each category of assets, for example, OT assets.
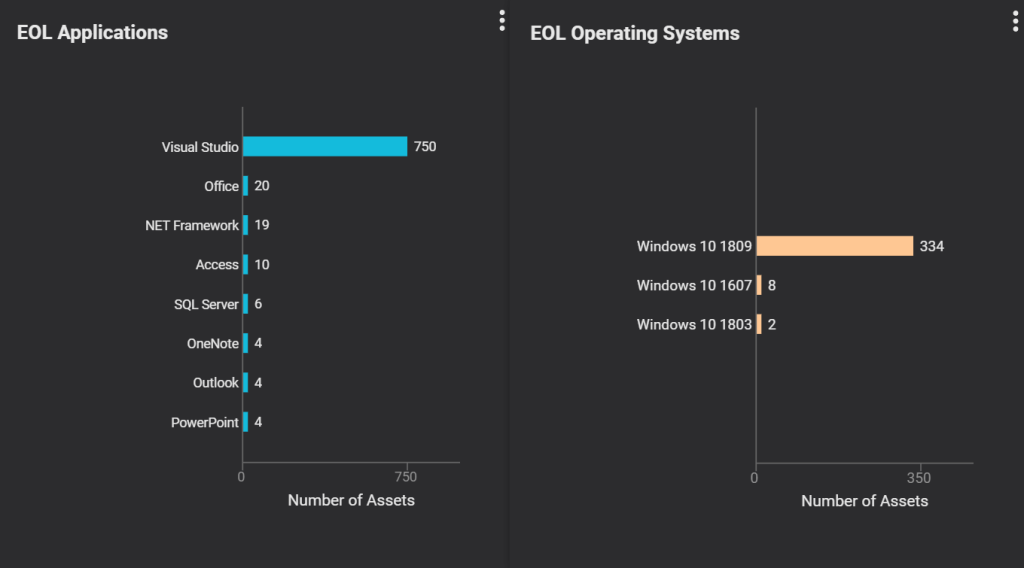
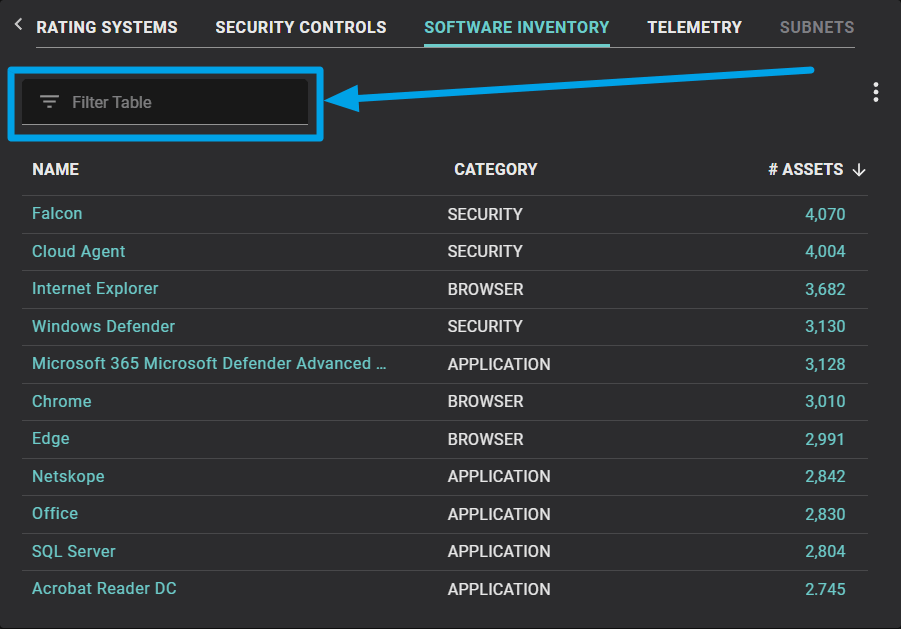
Identifying what software is installed on each asset is normally difficult, but Balbix simplifies this process by generating a comprehensive and instantly searchable software inventory automatically. Being able to see how many instances of software exist in your environment allows you to have insight into potential licensing violations. It can also provide you with a view of unpatched or end of life (EOL) software.
The image below shows a summary of EOL applications (left) and EOL operating systems (right). While this example shows a comprehensive software inventory, you could refine the chart to focus on servers, workstations, assets at a particular site or region, or by using another filter. No matter how you slice it, a view of EOL software provides IT and security teams with a quick and simple way to identify potentially at risk software and systems.
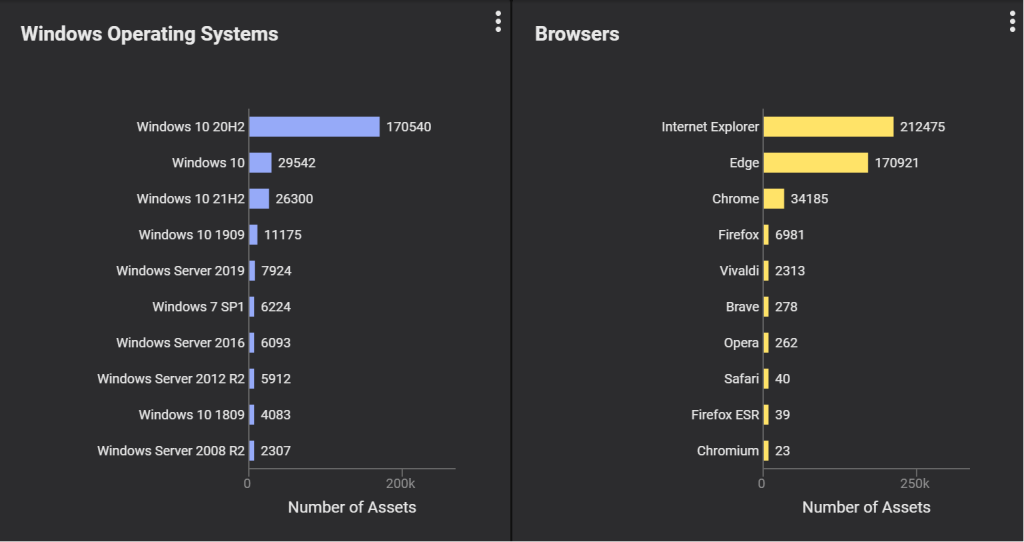
Another risk to your organization could come from employees downloading software that is in violation of company policy. The image below shows an inventory of two types of software – operating systems (OS) and browsers. You get a high level overview of what Windows OS versions and browsers employees have downloaded and deployed to help you inventory your software, and root out potential risk issues.
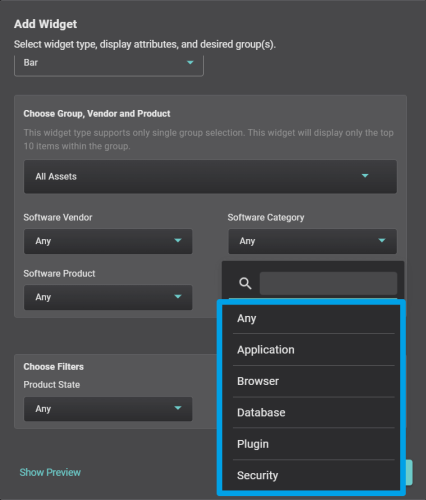
As you can see in the image below, you can use a simple menu-driven widget to break out your software inventory by vendor, category of software (OS, database, application, browser, plugin, or security), software product, or state of the software product (e.g. patched, unpatched, vulnerable or EOL).
In addition to the above charts, Balbix also provides you with the ability to search for any type of operating system or application. You can perform a search across your entire enterprise, or for a subset of your assets (e.g. only Linux servers, only systems with Tanium deployed, etc.). These searches can be helpful when you want to know how many systems are using a given application or the specific version of an application. This can be especially useful for zero day vulnerabilities when security teams need to quickly identify systems with affected software product(s) and apply mitigating controls.
The image below shows you how the search field is displayed in the Balbix UI.
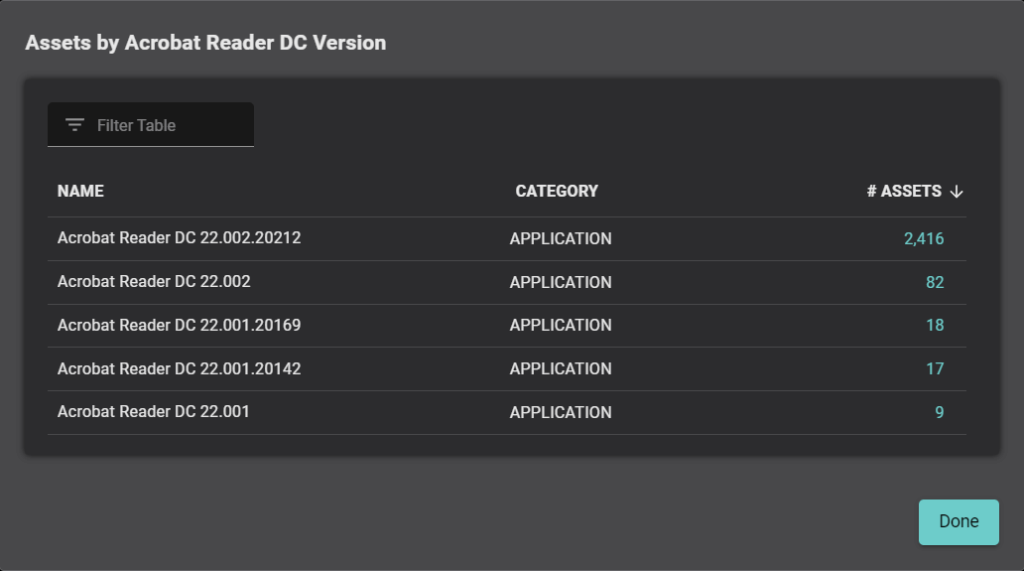
The image below illustrates how you can drill down even further into specific application versions, in this case for Adobe Reader, and see all versions present in your environment along with the number of assets which have that version installed. You can then click on the number of assets to get a comprehensive list of those systems.
Another benefit of Balbix’s CAASM solution is that it provides you with a unified view of your asset inventory across multiple cloud domains. You can quickly get asset inventory and risk insights across your Amazon Web Services (AWS) and Google Cloud Platform (GCP) assets and users. At any time, you can also filter your inventory for just AWS or GCP.
Balbix categorizes your assets into compute, K8s clusters/containers, storage, and other active cloud services. Balbix can catalog more than 400 attributes for each asset (depending on data sources) including general asset information, and information about its network, storage, open ports, system details, users, software inventory and any existing (or missing) security controls.
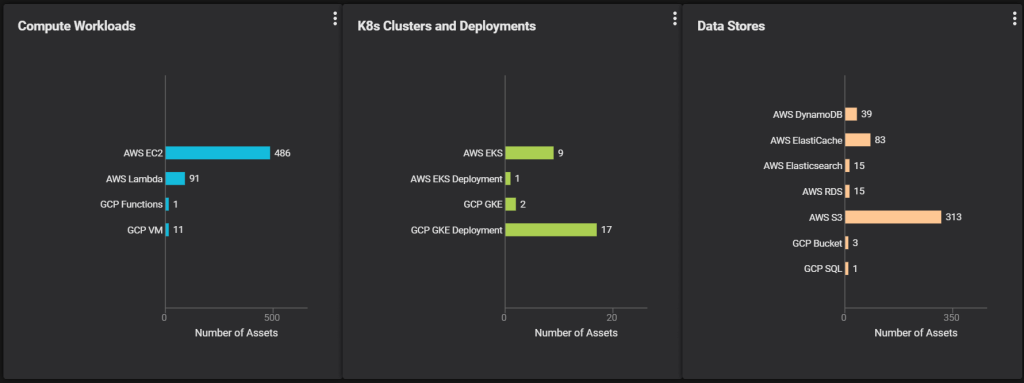
With a unified view of your environment – on premise, multi cloud or hybrid – your security and IT teams can respond quicker and make more informed and accurate decisions.
Ensuring your asset inventory is accurate and complete, especially across multiple platforms, is notoriously difficult. It is especially inefficient to manually pull together an inventory from multiple tools where each tool only offers a small slice of the complete picture. In contrast, the data aggregation and analytics capabilities of Balbix’s CAASM solution allows you to unify your asset inventory in a single place. Your inventory of assets and their associated attributes become searchable, with asset data and associated vulnerabilities being continuously updated in near real time.
Having an accurate and up-to-date inventory increases your productivity. It also allows you to cross reference dozens of tools in ways security and IT teams never thought possible, giving your organization the upper hand when it comes to protecting against attackers.