Attack Surface Management (ASM) is a cybersecurity strategy for identifying, assessing, and reducing cyber risks by managing all potential attack vectors in an organization’s systems. ASM starts with asset discovery, identifying all internet-facing assets such as web apps and cloud storage. It then performs vulnerability assessments to detect misconfigurations and weaknesses.
ASM helps prioritize and remediate vulnerabilities based on their potential impact and continuously monitors for new risks. By viewing the system from a hacker’s perspective, ASM enhances visibility and reduces the likelihood of successful cyberattacks, strengthening overall security and reducing the likelihood and impact of future cyber attacks.
What is an Attack Surface?
An attack surface is the total number of potential entry points or vulnerabilities in a network or system where attackers can attempt unauthorized access. It includes all hardware, software, and user interactions that cybercriminals could exploit to breach an organization. The attack surface consists of endpoints, applications, servers, and other digital assets vulnerable to attacks.
The broader an attack surface, the higher the exposure to threats. Managing and reducing the attack surface is critical to minimizing risk, preventing exploitation, and ensuring effective cybersecurity defenses for businesses and organizations.
Why is Attack Surface Management (ASM) Important?
Attack Surface Management (ASM) is crucial for organizations to mitigate cyber risks by minimizing their attack surface—the sum of all potential entry points for cyber threats. As enterprises adopt cloud technologies, enable remote work, and integrate third-party systems, their attack surfaces expand, creating more vulnerabilities that attackers can exploit. ASM helps secure these entry points by providing real-time visibility into assets, continuously monitoring for new vulnerabilities, and prioritizing remediation efforts based on risk levels.
With cyberattacks increasing in complexity, ASM is essential for reducing the likelihood of breaches and mitigating the damage if one occurs. By identifying high-risk vulnerabilities and addressing them before they can be exploited, ASM helps organizations enhance their security posture, ensuring comprehensive coverage of digital assets across cloud, mobile, and on-prem environments.
The Core Functions of Attack Surface Management
There are seven core functions in the attack surface management process. We dive into each of them below:
Asset Discovery
Effective Attack Surface Management (ASM) begins with asset discovery, which involves identifying and cataloging all assets across cloud, mobile, and on-premise environments. This process ensures that authorized and unauthorized devices, including shadow IT, are visible. Without real-time visibility into assets, security teams cannot address risks proactively. Tools like Wiz.io automate asset discovery, continuously tracking new or unmanaged devices as they appear, which helps reduce potential vulnerabilities.
Vulnerability Assessment
After identifying assets, the next step is performing vulnerability assessments. These assessments continuously scan and evaluate assets for weaknesses and security gaps. By understanding an organization’s infrastructure vulnerabilities, security teams can prioritize which ones need immediate attention. Regular assessments ensure new risks are promptly identified and addressed before they become exploitable.
Risk Prioritization
With numerous vulnerabilities detected, organizations must prioritize them based on business impact and likelihood of exploitation. By assigning a risk score to each vulnerability, ASM tools like Balbix help teams focus on the highest-risk vulnerabilities, ensuring resources are directed where they will have the most significant impact. Prioritization reduces the attack surface and mitigates potential cyber threats efficiently.
Continuous Monitoring
The dynamic nature of modern IT environments necessitates continuous monitoring of the attack surface. Real-time tracking of new vulnerabilities and changes ensures that security teams can stay ahead of emerging threats. Unlike static assessments, continuous monitoring provides ongoing visibility into an organization’s security posture, allowing for faster detection and response to potential risks.
Remediation
Remediation involves addressing and fixing vulnerabilities to reduce the attack surface. This can include applying patches, updating software, or reconfiguring systems. Automated tools streamline remediation processes, ensuring that high-risk vulnerabilities are addressed first. By integrating automated patch management, organizations can swiftly resolve security issues before they are exploited.
Stop Sabotaging Your Cybersecurity
Avoid the 11 common vulnerability management pitfalls
Threat Intelligence Integration
Incorporating threat intelligence into ASM helps organizations stay ahead of emerging threats. By understanding external threats, security teams can tailor their defenses and prioritize the most critical risks. This integration ensures that ASM strategies remain aligned with the latest developments in the cyber threat landscape, enhancing the overall security posture.
Automation
Automation is crucial for managing the sheer volume of assets and vulnerabilities in today’s complex environments. ASM tools powered by machine learning and AI automate asset discovery, risk prioritization, and remediation processes. This allows organizations to respond to threats faster and more efficiently, improving overall security and reducing manual workloads.
Benefits and Challenges of Attack Surface Management
Attack Surface Management (ASM) is essential for securing modern organizations by providing real-time visibility into assets and vulnerabilities across diverse environments, including cloud, mobile, and shadow IT.
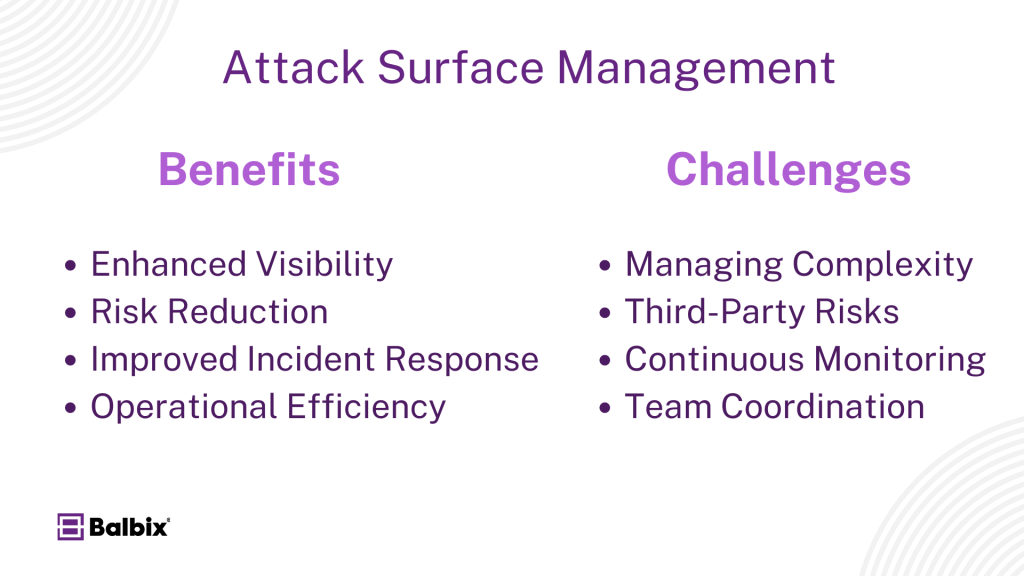
The following are some benefits and challenges of ASM:
Attack Surface Management Benefits
- Enhanced Visibility: ASM provides real-time visibility into all assets, including shadow IT and unmanaged devices, ensuring security teams can proactively address risks. This is critical for a complete view of the attack surface, especially in cloud and mobile environments.
- Risk Reduction: By prioritizing vulnerabilities based on business impact, ASM ensures that high-risk vulnerabilities are remediated first, reducing the attack surface and minimizing the likelihood of successful cyberattacks.
- Improved Incident Response: Continuous monitoring helps organizations detect and mitigate threats faster, improving incident response times and reducing potential damage during an attack.
- Operational Efficiency: Automation reduces manual workloads for asset discovery and vulnerability assessment, allowing security teams to focus on higher-priority tasks and improve overall efficiency.
Attack Surface Management Challenges
- Managing Complexity: The growing diversity of IT environments, including cloud and IoT, makes maintaining visibility across all assets challenging, especially as attack surfaces expand with new technologies.
- Third-Party Risks: Organizations often struggle to manage risks from third-party vendors, as vulnerabilities in partner systems can expose the organization to significant risk without direct control.
- Continuous Monitoring: Real-time asset visibility can be resource-intensive, requiring robust infrastructure and automation to avoid gaps in security coverage.
- Coordination Across Teams: Effective ASM requires collaboration between IT, security, and risk management teams, which can be difficult if these teams operate in silos. Cross-team coordination is key for a unified security approach.
Using Cyber Asset Attack Surface Management
Cyber Asset Attack Surface Management (CAASM) plays a crucial role in modern cybersecurity by automating the discovery and management of assets across cloud, mobile, and network environments.
By leveraging API integrations, CAASM enables security teams to consolidate data from various security tools, providing a clear and real-time view of the organization’s attack surface. This automation identifies vulnerabilities and gaps in security controls, improving response times and overall security hygiene. CAASM ensures organizations maintain up-to-date visibility into their assets, reducing the risk of missed vulnerabilities.
Another vital function of CAASM is its integration with risk management strategies for holistic security coverage. CAASM helps organizations prioritize vulnerabilities by providing insights into asset criticality and breach likelihood.
When used with risk management, CAASM helps organizations improve cyber resilience by focusing on the assets that pose the most significant risk. The combination of automated asset discovery and strategic risk assessment helps companies proactively manage their exposure, ensuring comprehensive security coverage across all digital assets.
With CAASM, Organizations can enhance their cybersecurity posture, reduce manual asset management tasks, and integrate security efforts seamlessly with risk management practices.
CAASM with Balbix
Balbix’s Cyber Asset Attack Surface Management (CAASM) solution is designed to provide organizations with comprehensive visibility and control over their entire attack surface. It automates the discovery, inventory, and continuous monitoring of all digital assets—both internal and external—across cloud, mobile, and on-premise environments. By aggregating data from various existing security tools and leveraging advanced AI, Balbix helps organizations gain a real-time, up-to-date understanding of their assets and potential vulnerabilities.
Frequently Asked Questions About Attack Surface
- What is ASM in security?
-
Attack Surface Management (ASM) is the process of identifying, monitoring, and mitigating external digital assets that could be vulnerable to cyber threats. ASM helps security teams continuously assess and reduce the attack surface, ensuring potential risks are detected and prioritized before they can be exploited.
- What is the difference between ASM and BAS?
-
ASM focuses on identifying and managing the external attack surface continuously monitoring digital assets. Breach and Attack Simulation (BAS) tests the effectiveness of security measures by simulating real-world attacks. While ASM maps potential entry points, BAS evaluates how well defenses respond to those threats.
- What is the difference between vulnerability management and attack surface management?
-
Vulnerability management (VM) addresses internal weaknesses by identifying and remediating organizational software vulnerabilities. Attack Surface Management (ASM) focuses on external assets and the broader attack surface, continuously identifying risks from exposed digital assets to mitigate potential entry points. Together, they provide a comprehensive defense against internal and external threats.


