When a new type of security product hits the market, it doesn’t typically belong to a defined “category.” Over time, as the product gains widespread use, and as new competitors emerge, a category will be defined. Analysts, journalists, and a wide range of infosec professionals start referring to these products in this way, and a narrow definition of that category becomes commonly accepted.
The challenge is that these definitions get ingrained into our minds, and while the needs of the enterprise will change over time, the definition is much slower to change. This is how we end up with silly terms like “next-gen firewall,” a category of products that has been around for 10 years, yet is still somehow next-gen.
This is also the case for vulnerability management and vulnerability scanners. According to the dictionary, a vulnerability is, “the quality or state of being exposed to the possibility of being attacked or harmed, either physically or emotionally.” This is a very broad term. Yet, somehow, in infosec, we’ve come to narrowly associate security vulnerability with unpatched software and misconfigurations.
The reason is that 20+ years ago (think pre-Google), when traditional vulnerability management vendors were getting their start, they focused on unpatched software and misconfiguration, the press and analysts branded this functionality, “vulnerability management,” and here we are 2 decades later living with that definition. We even have a de facto standard severity ranking system, CVSS scores, that handle only this narrow definition.
The problem is that not every vulnerability is a CVE with a corresponding CVSS score.
The 9 Types of Security Vulnerabilities:
- Unpatched Software – Unpatched security vulnerabilities allow attackers to run a malicious code by leveraging a known security bug that has not been patched. The adversary will try to probe your environment looking for unpatched systems, and then attack them directly or indirectly. –
- Misconfiguration – System misconfigurations (e.g. assets running unnecessary services, or with vulnerable settings such as unchanged defaults) can be exploited by attackers to breach your network. The adversary will try to probe your environment looking for systems that can be compromised due to some misconfiguration, and then attack them directly or indirectly.
- Weak Credentials – An attacker may use dictionary or brute force attacks to attempt to guess weak passwords, which can then be used to gain access to systems in your network.
- Phishing, Web & Ransomware – Phishing is used by attackers to get users to inadvertently execute some malicious code, and thereby compromise a system, account or session. The adversary will send your users a link or malicious attachment over email (or other messaging system), often alongside some text/image that entices them to click.
- Trust Relationship – Attackers can exploit trust configurations that have been set up to permit or simplify access between systems (e.g. mounted drives, remote services) to propagate across your network. The adversary, after gaining access to a system, can then proceed to breach other systems that implicitly trust the originally compromised system.
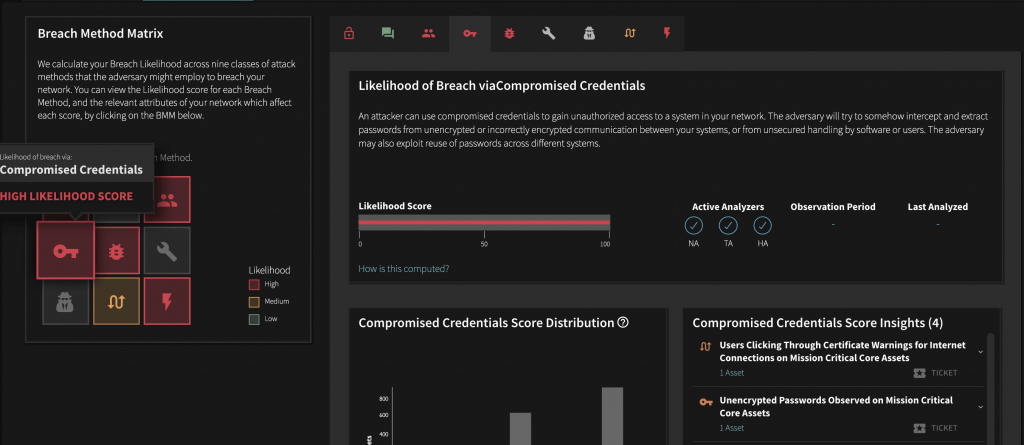
- Compromised Credentials – An attacker can use compromised credentials to gain unauthorized access to a system in your network. The adversary will try to somehow intercept and extract passwords from unencrypted or incorrectly encrypted communication between your systems, or from unsecured handling by software or users. The adversary may also exploit reuse of passwords across different systems.
- Malicious Insider – An employee or a vendor who might have access to your critical systems can decide to exploit their access to steal or destroy information or impair them. This is particularly important for privileged users and critical systems.
- Missing/Poor Encryption – With attacks on Missing/Poor Encryption, an attacker can intercept communication between systems in your network and steal information. The attacker can intercept unencrypted or poorly encrypted information and can then extract critical information, impersonate either side and possibly inject false information into the communication between systems.
- Zero-days & Unknown Methods – Zero days are specific software security vulnerabilities known to the adversary but for which no fix is available, often because the bug has not been reported to the vendor of the vulnerable system. The adversary will try to probe your environment looking for systems that can be compromised by the zero day exploit they have, and then attack them directly or indirectly.
Balbix looks at all 9 classes of security vulnerabilities, automatically and continuously calculating likelihood of breach via each class for every asset on your network. The result is mapped to the Balbix Breach Method matrix, and used as part of the risk calculation score that feeds actionable, prioritized insights to help your team maximize cyber resilience.