This is post 5 in our series on making infosec jobs easier and covers how cybersecurity teams can adjust to changes in IT landscape. The first post covered improving overall security posture. The second post discussed assessing and reporting on breach risk. The third post was all about keeping systems patched. The fourth post covered how to adjust to changes in the IT landscape.
It is no secret that data is growing fast. Every person in the U.S. owned an average of 3.47 network-connected devices in 2015. By 2018 that number had more than doubled to 8 devices per person. Experts predict that number will climb to 13.6 by 2022.
The growing number of devices and apps present a major challenge for enterprises. No infosec team has the resources to protect these assets and keep track of the corresponding exponential data growth. If defending the enterprise from outside threats wasn’t difficult enough, infosec teams must also account for the behavior, both benign and malicious, of insiders that put the enterprise at risk.
The problem is that many organizations don’t have a real-time view of which users have access to which data. In fact, most organizations struggle to gain an inventory of the devices being used to access data, let alone the data itself. Lack of visibility into data access creates a major security blind spot.
User behavior is also a big question mark for many enterprises. If a malicious insider were to transfer data outside of the enterprise, no one would know. The lack of visibility into user data access and privileges would further complicate the matter, making it difficult to investigate data theft or leaking without intensive forensics.
Luckily, there are numerous security controls that help prevent data loss and fraud. These can mitigate the risk of data loss substantially. But despite big investments in point products, many organizations don’t know exactly where these products are reducing risk because they don’t have complete visibility into their attack surface.
The Consequences of Data Loss
In some cases, data loss can be a minor setback for a business. In other cases, it can create irreparable damage.
A high-profile data loss event occurred recently when fitness brand V Shred left personal information of 99,000 people on an unsecured AWS S3 bucket. This exposure of confidential information creates an increased risk of fraud and phishing attacks for their customers. The event has not only shredded V Shred’s brand reputation, but tarnished customer loyalty.
Data loss events that don’t affect customers often impact a company’s daily processes. If a business unit’s productivity is impacted for hours, days, or weeks because of data loss, the financial consequences are severe. In the worst cases, major data loss events can even cause businesses to fail.
Preventing Data Loss and Fraud
The rapid, exponential growth of data has left humans helpless in tracking and preventing data loss on their own. In today’s enterprise, the job of preventing data loss and fraud is fraught with challenges.
With the help of these technologies, here are 3 steps you should take to prevent data loss and fraud:
- Discover critical assets and users that have access to them
- Analyze user behavior, access privileges, critical assets, and existing compensating controls
- Execute on a comprehensive strategy by prioritizing risk items, assigning and educating owners, addressing risk, and tracking progress
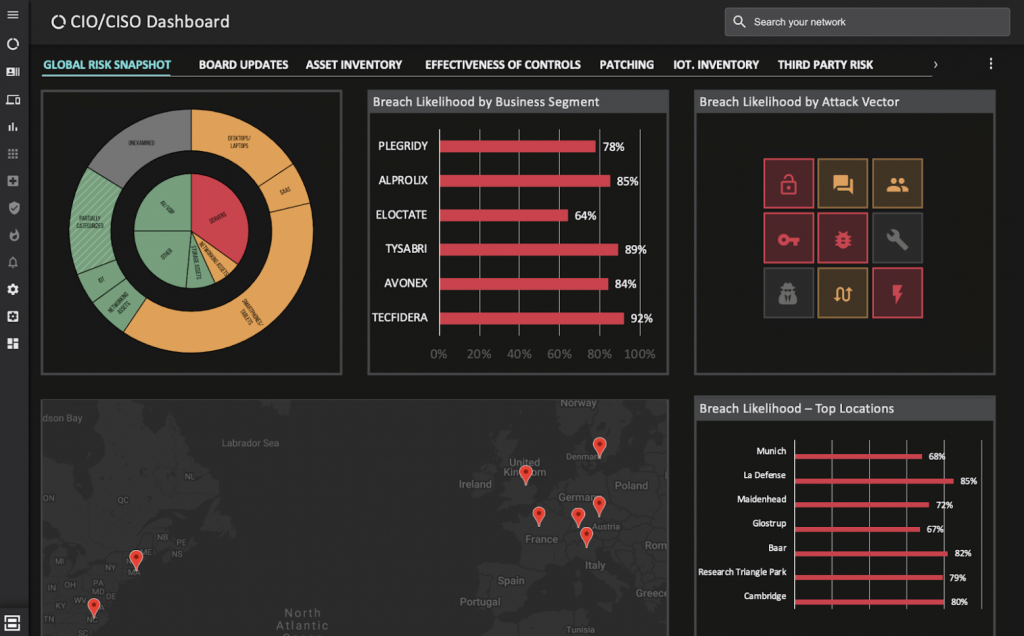
Balbix can help with each of these steps, making your job of preventing data loss and fraud easier. The system automatically discovers your entire IT asset inventory and analyzes the impact that a breach would have at every point in real time. Google-like natural language search makes it easy to investigate access privileges for specific devices and the vulnerabilities on business critical applications that are creating the most risk. With dashboards that feature prioritized risk insights and drill-down heatmaps, you have everything you need to prevent data loss and fraud in your enterprise.
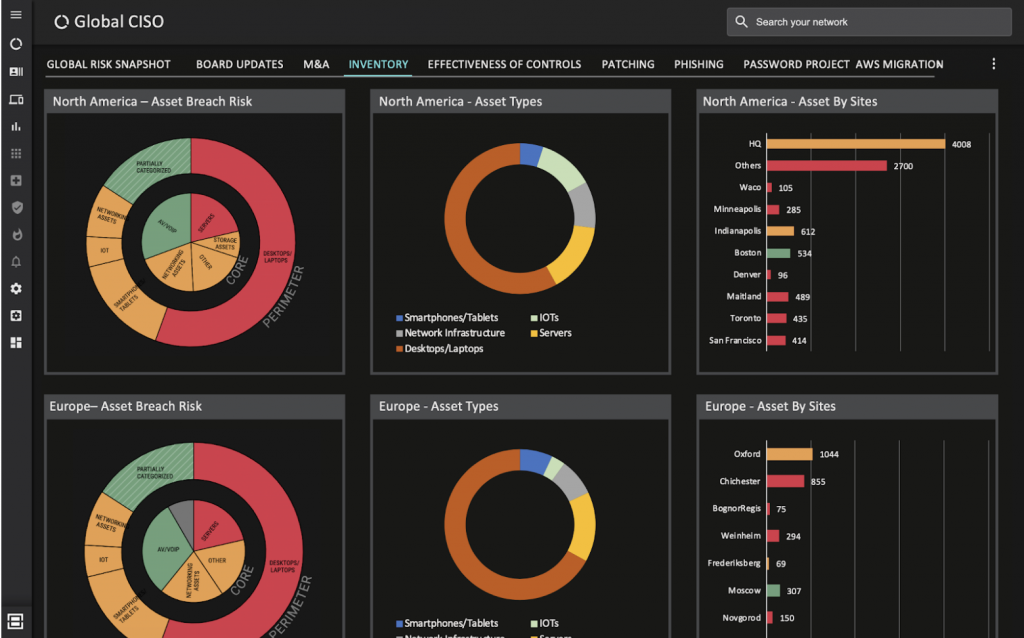
With Balbix, you can easily keep a real-time dashboard of your inventory, broken down by asset types or location.
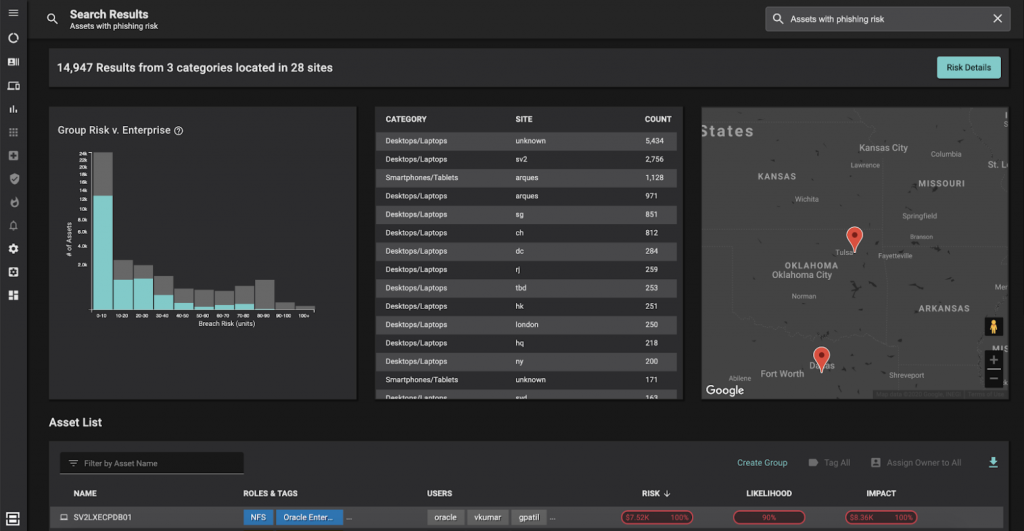
Identify users at risk of phishing with natural language search. Use filters to pinpoint specific groups like admins.
Or snapshot your risk by business segments, locations, and across attack vectors.
Request a demo today to learn more about these and other capabilities in the Balbix platform.