

February 23, 2022
There was a time when asset management was primarily the concern of IT teams tasked with collecting and maintaining asset inventory, managing asset licenses, and upgrading, retiring or decommissioning assets.
However, with the increase in digital workplaces, cloud, and IoT, and the heightened risk these assets represent to an organization, security teams increasingly need to pay more attention to asset management.
Yet, traditional IT asset management tools fall short of what most security teams need to properly manage risk. For example, legacy asset management tools lack real-time information which is critical for security analysts to identify assets with vulnerabilities currently being exploited. Another shortcoming is the lack of any risk and business context making it difficult for both the security and IT teams to prioritize remediation efforts.
In large organizations, security teams have the additional challenge of having a unified asset view as IT teams often use different asset management tools for different parts of the network, for example on-premises assets versus cloud environments.
Balbix asset inventory capabilities are designed to address the limitations of traditional IT management tools and empower both security and IT teams through automation and AI. Balbix automates the collection of asset data across the entire enterprise from existing IT and security tools (CMBD, EDR, vulnerability management, Active Directory, and Cloud/IaaS) giving you a single, unified, real-time view of your asset inventory. Any conflicting and duplicate data is cleaned and merged automatically. Automating the asset identification and collection process also helps to reduce cost and errors.
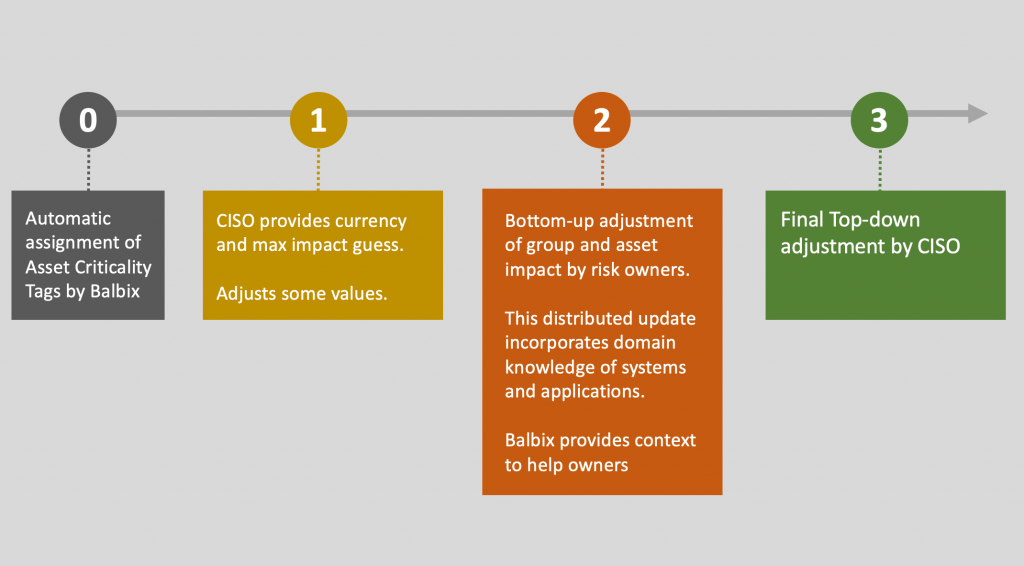
Balbix goes beyond merely collecting and unifying asset information. Balbix adds business-criticality and risk context to your asset information making it easy for your security and IT teams to prioritize the most critical assets to your business. Contextual properties include asset type (mission critical, privileged, etc.), the risk inherent in the role of the asset (including a risk to intellectual property, a risk to customer data, or a risk of operational disruption, for example), user privileges and an asset’s interaction with other assets.
Balbix identifies over 400 attributes about any given asset including asset type, usage, risk owner, location, software versions and vulnerabilities. Balbix can even identify specific application processes which are critical for hard to find vulnerabilities such as Log4Shell, a zero-day vulnerability in the Java logging tool Log4j. In fact, Balbix helped a Fortune company reduce the time they took to find and remediate Log4j instances from months to weeks.
In addition, Balbix uses intelligent tagging to make it easier for users to search your asset inventory in a risk and business language they understand such as “iOS devices in Mountain View susceptible to Spectre” or “unpatched DNS servers in Texas” and get the answers quickly.
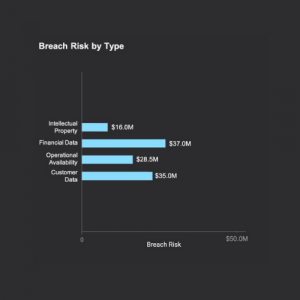
Balbix also automatically calculates breach risk in monetary terms. Breach risk is the product of breach likelihood (measure a percentage) and breach impact (measure in monetary terms such as dollar, yen or euros). Breach likelihood is based on several factors such as network traffic, exposure, vulnerabilities, security controls, and compensating controls. Balbix breach impact is quantified in dollars (and other currencies) and considers cost categories including detection and escalation, notification, post breach response, lost business cost.
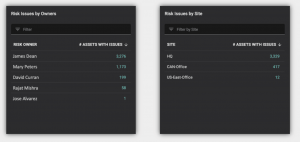
Balbix also aligns security, IT, and business owners by providing actionable dashboards to each risk owner with inventory information specific to their asset domain. Timely notifications can also be delivered to risk owners to ensure remediation efforts stay on track.
To see how you can leverage and enhance your existing IT asset management tools for use by the security team, we invite you to schedule a demo of the Balbix Security Cloud.