Yesterday, Balbix and Cybersecurity Insiders published the 2020 State of Security Posture Report, revealing key findings around the attitudes that infosec teams have about their security posture and the biggest challenges they face when trying to improve it. Most notably, 64% of organizations say they are, at best, somewhat confident in their security posture. The following findings in the report give a better idea of why this is the case.
Fuzzy security visibility appears to be commonplace for the average enterprise. Forty-six percent of respondents find it hard to tell which vulnerabilities are real threats versus ones that will never be exploited. Only 13% of respondents were not concerned about their current security visibility.
The most important building block of any visibility program is an accurate inventory of what you are defending. Unfortunately, it is quite hard to keep track of the various devices, applications, and services used by enterprise users. As a result, it is difficult to correctly target vulnerability scans and risk assessments. It is particularly problematic to cover non-traditional assets such as bring-your-own devices, IoT, mobile assets, and cloud services.
Gaps in asset coverage are leaving cybersecurity leaders with more questions than answers about their security posture. Sixty-percent of organizations are aware of fewer than 75% of the devices on their network. This is a significant issue because without an accurate and up-to-date inventory, organizations will struggle to improve security.

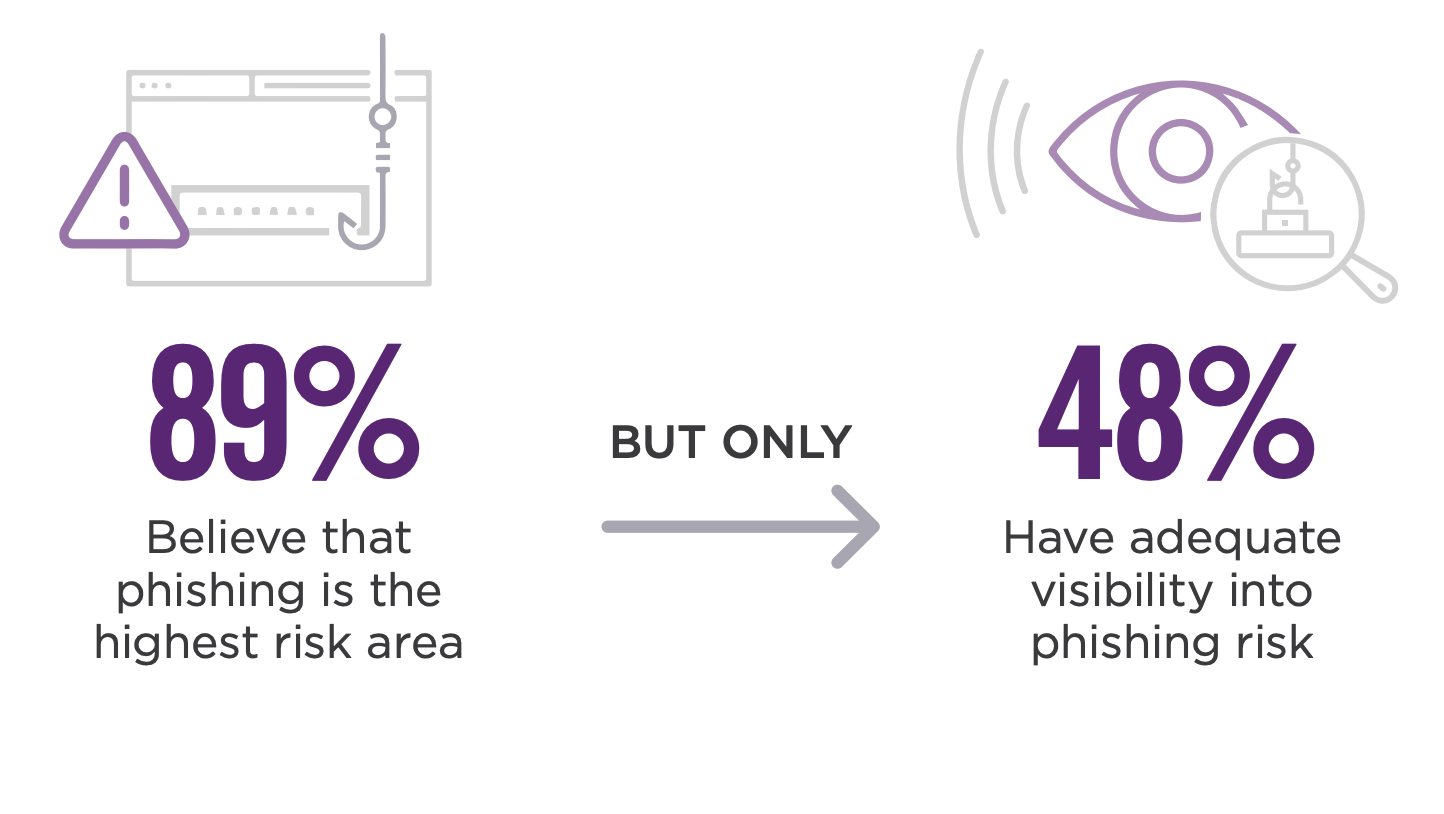
An enterprise is only as secure as its weakest link. For many organizations, that weak link is users at high-risk of phishing. Phishing dominated the biggest risks to organizations surveyed for the report with 89% saying it was driving the most risk, followed by unpatched systems and misconfiguration. Although nearly 9 out of 10 said that phishing was their highest risk area, only under half (48%) said that they had adequate visibility into it.
One of the reasons that phishing drives so much risk to organizations is because the user who gets phished serves as a catalyst for the attacker to move laterally in the infrastructure and create a larger breach. This problem is accentuated by the fact that 81% of organizations report users with too many access privileges. When access privileges for business critical assets are not closely monitored, the likelihood of a major breach grows substantially.
With the numerous security posture issues that Infosec leaders face, it should not be surprising that board presentations are a major challenge. When asked how their last board or senior management presentation went, only 13% of respondents said they nailed it. The majority (52%) said that their presentation went okay. They had a good discussion and got their point across, but it didn’t have the outcome they expected.
These findings point to a larger issue – cybersecurity leaders do not have adequate resources to assess, improve and report on their security posture.
They need visibility into all the devices and applications on their network, as well as the 100s of attack vectors they are susceptible to. This visibility should be continuous, as periodic scans go quickly out of date. Infosec teams should also have visibility into the overall risk associated with open vulnerabilities to know if they are real threats or just noise.
With 81% of organizations providing more access privileges than necessary for their users, it is critical to have visibility into the threats affecting these users. Vulnerabilities on privileged user assets should be treated with urgency and given high priority, since exploitation will result in an accelerated breach. Organizations should also take steps to limit access privileges where possible.
The majority of cybersecurity leaders are settling for “okay” board presentations when they could be nailing it. Effective board-level presentations start with quantifiable risk metrics and intuitive visualizations. They should focus on business objectives and help stakeholders understand where the company is on cyber risk, where it should be, and how it can get there.
