

February 16, 2022
Are you curious about how your cybersecurity posture compares to your peers? Read on, we have some answers for you. Balbix and Cybersecurity Insiders recently conducted a survey on cybersecurity posture management challenges and concerns. The 2022 State of Cybersecurity Posture Report is based on survey responses from ~300 IT and cybersecurity professionals in the US. The respondents ranged from technical executives to IT security practitioners, representing a balanced cross-section of organizations of varying sizes across multiple industries.
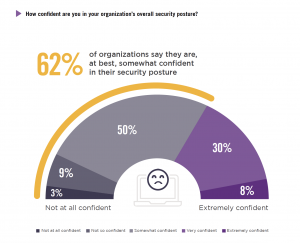
The report revealed that 62% of organizations are not confident in their security posture. Cybersecurity leaders struggle to communicate their security posture to the board and senior management and to justify investment in cybersecurity staff and controls.
Other key findings in the report include:
These findings confirm what we have observed firsthand at Balbix through conversations with CISOs, and other infosec leaders and practitioners. For example, when asked about his security posture challenges, Francois Lepage of the Master Group said, “we didn’t have a good source of authority on all the IP connected devices in our environment and we didn’t have appropriate asset classification. Our vulnerability scans took such a long time to run and when finished, there was a lack of prioritized information on which vulnerabilities and systems to address and patch first. As a result, by the time I received the report, the information was already out-of-date.”
52% of cybersecurity leaders are settling for “okay” board presentations when they could be nailing it. Effective board-level presentations start with quantifiable risk metrics and intuitive visualizations. They should focus on business objectives and help stakeholders understand where the company is on cyber risk, where it should be, and how it can get there.
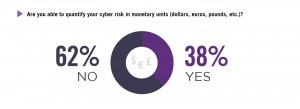
Having the appropriate business metrics to discuss with the board is key. However, 62% of respondents said that they are not able to calculate their breach risk in monetary terms. As a result, it is challenging to catch the attention of the board and enable them to make the right decisions when it comes to security investments. Calculating cyber risk in monetary terms provides a common language that organizations – from security engineers and IT admins to the CISO, CFO and CIO – can use to prioritize projects and spending and track the effectiveness of their overall cybersecurity program.
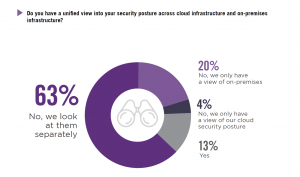
To quantify cyber risk, security teams need to have enterprise-wide visibility across their hybrid cloud environments. Today, that is rarely the case. 63% organizations view their cloud and on-premises assets through separate dashboards and 20% only have a view of their on-prem assets. Organizations need to merge cloud and on-premises visibility in one view, eliminating the need for security practitioners to look through multiple dashboards and allowing them to work more productively.
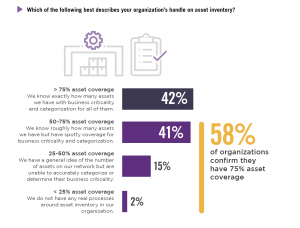
Another challenge for respondents was having an incomplete asset inventory. Most survey respondents, 58%, were aware of fewer than 75% of assets on their network. Unlike IT teams, security teams need continuous, comprehensive visibility of real risks to their organization. This starts with an accurate asset inventory based on the continuous real time monitoring of assets for vulnerabilities, and from there, prioritizing fixes for the riskiest issues.
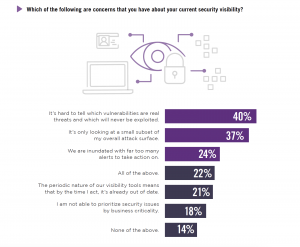
Survey respondents also had a range of concerns about their current security visibility. They are struggling with a lack of cybersecurity visibility despite having dozens of cybersecurity tools. Additionally, depending on the size of their enterprise, they often find it impossible to mitigate all vulnerabilities, given their sheer volume, across the myriad attack vectors. Prioritization would help but, organizations say they are unable to prioritize mitigation actions based on business risk.
You can read the full 2022 State of Security Posture Report here.
Balbix provides the world’s leading platform for cybersecurity posture automation. With the advanced analytics and automation of the Balbix Security Cloud, security teams can accurately inventory their cloud and on-premises assets, conduct risk-based vulnerability management, and quantify their cyber risk in monetary terms.
