May 10, 2023
The Derby has been run, summer is nearly here, and the flowers are blooming… but so are the Microsoft security vulnerabilities. So, time to grab your shears and tend your infrastructure garden by addressing this month’s Patch Tuesday issues.
This month, Microsoft announced fixes for 38 new CVEs including 6 Microsoft-rated critical vulnerabilities, 2 new zero-day vulnerabilities (CVE-2023-29344 & CVE-2023-29333), 1 update to a previously reported exploitable vulnerability (CVE-2013-3900) as well as 12 other updates to previously released CVEs.
Of the 38 new vulnerabilities, the fix sources break down as follows:
The headline issues this month are the two new known exploitable zero-day CVEs:
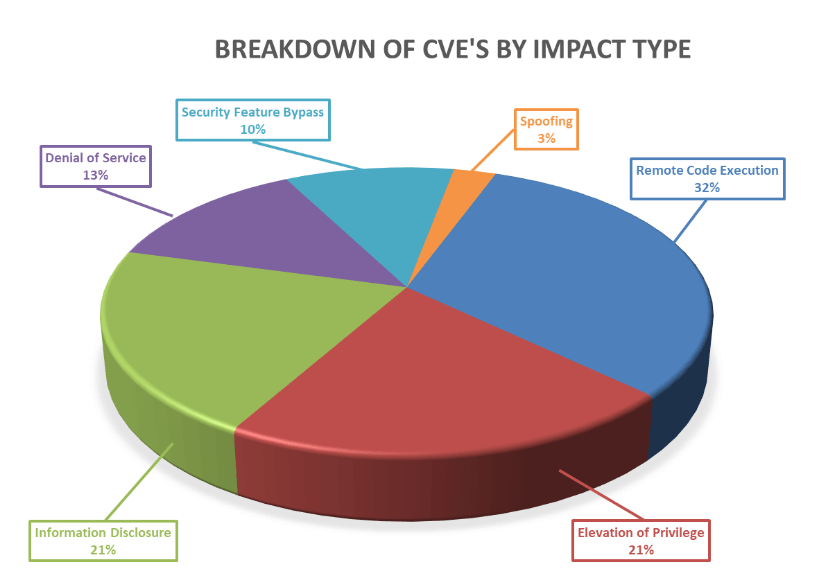
Breaking down the 38 vulnerabilities further by impact type, we can see that remote code execution leads the way again this month with elevation of privileges and information disclosure tied right behind it.
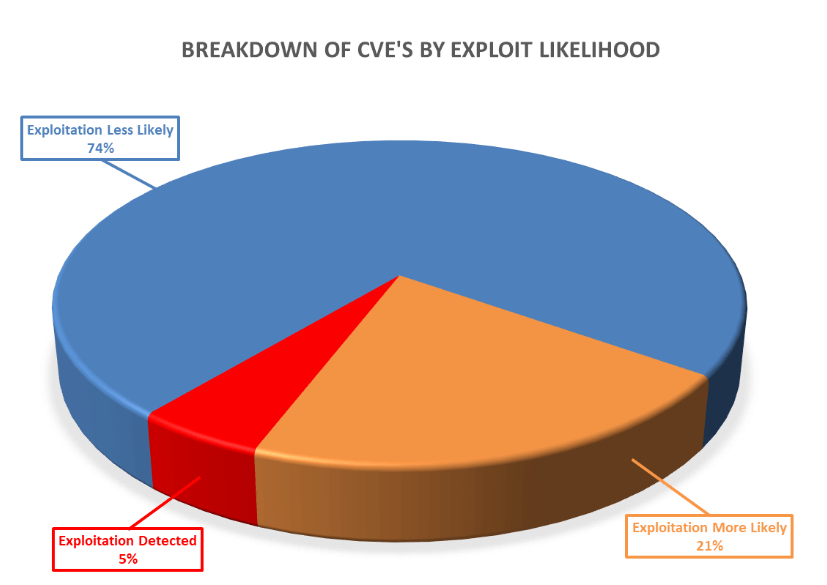
Furthermore, as can be seen below, these vulnerabilities vary in terms of how likely they are to be exploited, with 26% of the vulnerabilities this month either already exploited or highly likely to be exploited as ranked by the Microsoft Exploitability Index
As always, Balbix can identify all affected assets within hours of release. There are no scans to run. Balbix customers simply search for the CVE name in their Balbix dashboard to view the list of affected assets. Filtered search functionality can also be used to search for the CVE by site, subnet, location, or other distinguishing factors.