
December 14, 2022
‘Tis the Season, and well, this month we continue to get the gift that keeps on giving, Microsoft Patch Tuesday! Yes, truly a joyous time for gathering around the keyboard with friends and colleagues to make sure that, at least for the next 30 days, we have a warm feeling from doing our part to secure cyberspace. OK, so I jest a bit. As we all know, cybersecurity goes far beyond simply patching your Windows system. However, given the global scope and pervasiveness of the Microsoft operating system and applications, applying these patches is indeed a critical function to which we must pay close attention.
This month there are 48 vulnerabilities, including 6 deemed critical, 1 zero-day and 1 advisory. The headline issues this month are:
These two vulnerabilities are featured for very different reasons.
CVE-2022-44698 is a known exploited vulnerability which affects Microsoft Defender SmartScreen functionality. This functionality is used to scan and analyze web pages as they are visited to determine if the site is potentially dangerous: suspiciously coded, or a known phishing or malware site. The exploitation of this vulnerability would be relatively simple and could be done by coaxing a user to visit a website or click on an email link that hosted code that exploited this vulnerability.
CVE-2022-41076 has the potential to allow an attacker to escape the PowerShell environment and escalate privileges. While attack complexity is indeed high, it requires no interaction from the user and no elevated privileges to execute.
Microsoft also released updates to the 8 other existing CVEs listed below:
| Orig. Release Date | CVE Number | CVE Title |
| Aug 9, 2022 | CVE-2022-34704 | Windows Defender Credential Guard Information Disclosure Vulnerability |
| Nov 8, 2022 | CVE-2022-37967 | Windows Kerberos Elevation of Privilege Vulnerability |
| Nov 8, 2022 | CVE-2022-41078 | Microsoft Exchange Server Spoofing Vulnerability |
| Nov 8, 2022 | CVE-2022-41079 | Microsoft Exchange Server Spoofing Vulnerability |
| Oct 11, 2022 | CVE-2022-38032 | Windows Portable Device Enumerator Service Security Feature Bypass Vulnerability |
| Oct 11, 2022 | CVE-2022-38042 | Active Directory Domain Services Elevation of Privilege Vulnerability |
| Oct 11, 2022 | CVE-2022-41043 | Microsoft Office Information Disclosure Vulnerability |
| Sep 13, 2022 | CVE-2022-37958 | SPNEGO Extended Negotiation (NEGOEX) Security Mechanism Remote Code Execution Vulnerability |
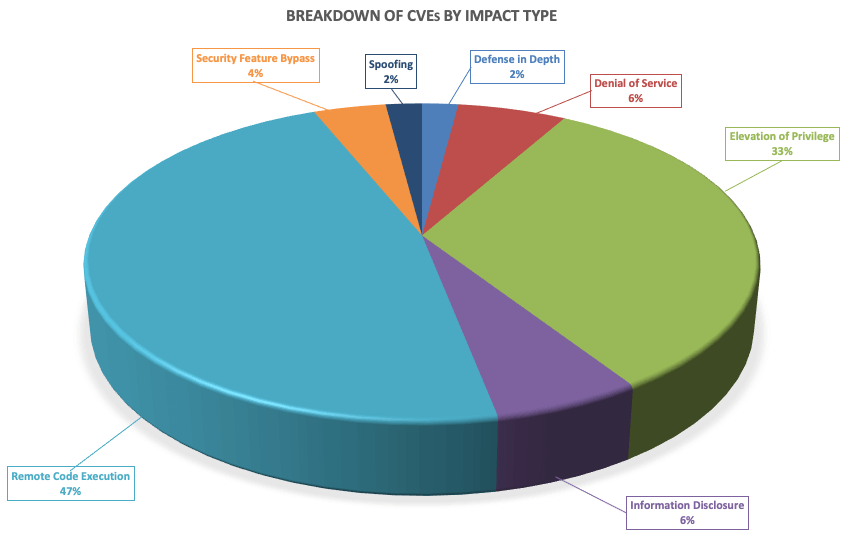
Breaking down the 48 vulnerabilities further, we can see that elevation of privileges and remote code executions lead the way this month in terms of impact type.
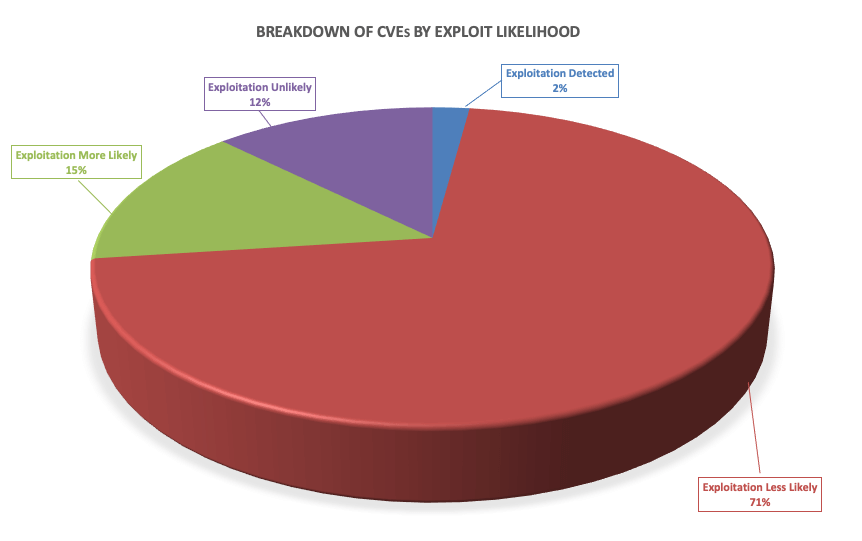
These vulnerabilities vary in terms of how likely they are to be exploited, with 17% of the vulnerabilities this month either already exploited or highly likely to be exploited.
As always, Balbix can identify all affected assets within 1 hour of release. There are no scans to run. Balbix customers simply search for the CVE name in their Balbix dashboard to view the list of affected assets. Users can also use the filtered search functionality to search for the CVE by site, subnet, location, or other distinguishing factors.