Most breaches happen because organizations only have a vague understanding of their security posture. That said, getting an accurate and up-to-date view of your attack surface and posture is no easy feat. There are an overwhelming number of assets in today’s enterprises and 100s of ways in which you can get breached.
Although the typical enterprise attack surface is rapidly changing, there are a few key components we can focus on to get a better idea of how we’re doing on cybersecurity. These 4 elements are key to cybersecurity posture, and will be the building blocks for organizations setting out on the security posture transformation journey.
- Inventory
- People/Users
- Security controls
- Network configuration and segmentation
In this post, the first of a four part blogger series, we’ll focus on inventory management and why it is critical to understanding your cybersecurity posture and driving your remediation strategy.
Asset Inventory Accuracy
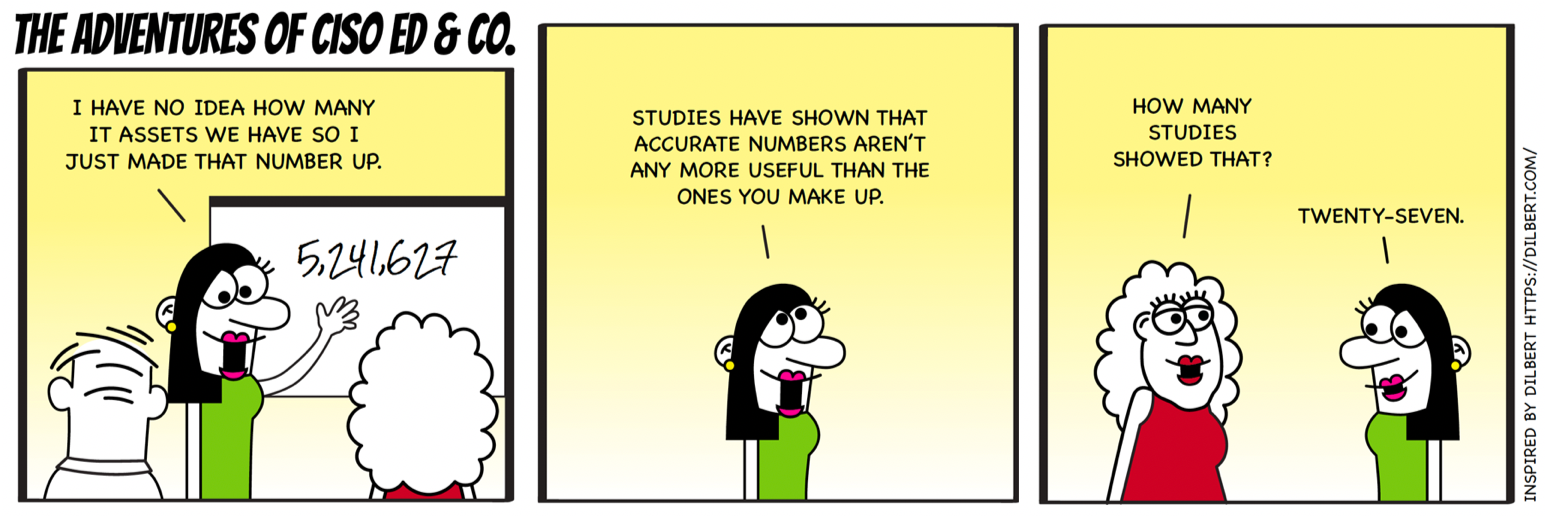
If you don’t know what you have, how can you defend it? Keeping an accurate and up-to-date inventory of assets is a challenge that most security teams struggle with. The set of assets in the enterprise changes constantly with devices being added and retired, physical machines migrating to virtual and various stakeholders constantly installing and updating software.
The CIS Top 20 security controls dictate continuous inventory of both hardware and software assets as the top 2 items to address. Many organizations over-rely on their Configuration Management Database (CMDB) for these metrics and yet openly admit inaccuracy due to the manual efforts required and ephemeral nature of the enterprise.
Inaccurate inventory also makes managing compliance very difficult. Key to effective data governance and compliance is an accurate and up-to-date inventory of your enterprise’s data, categorized by departments and/or risk owners. Furthermore, you need to know which assets are holding highly sensitive information like customer PII or intellectual property.
To put it in a few words, the accuracy of your inventory will be a driving force for the high-level understanding of risk and resource allocation in your organization.
IT Asset Categorization
The ability to categorize IT assets based on a multitude of characteristics is essential for keeping a firm grasp of your attack surface. These could be attributes such as asset type, usage, risk owner, location, software version or vulnerabilities its affected by. Being able to quickly view and create dynamic groups for assets by your category of interest is crucial for answering difficult questions about your security posture..png)
More advanced security posture platforms go beyond basic categorization and also categorize assets based on business criticality and breach likelihood. While traditional inventorying methods focus on quantities and typically view all assets as equally important, tools like Balbix provide inventory with business context. This means that assets that store sensitive data, provide critical services such as web servers and domain controllers, or that various business systems rely on are given greater emphasis.
Inventory Searchability
If you needed to quickly discover all of your IT assets susceptible to the new Maze Ransomware, how long would it take your team to do it? 3rd generation cybersecurity solutions like Balbix make searching your inventory as user-friendly as searching on Google for a good dinner recipe.
With an overwhelming amount of assets to keep track of, you should be able to quickly find assets in your inventory using simple queries like “windows servers in Boston” or “unpatched mission critical assets.” For threat hunting purposes, you should also be able to search assets by CVE number or virus names like “wannacry” to see where you are susceptible to breach.
Part 2
In Part 2 of this blog series, we’ll look at an essential component of security posture that often gets overlooked: people. How can organizations protect their perimeter from user induced vulnerabilities?
