Let’s get straight to the point. The main question your board has is, “Are we secure?” As you know, that is an overly simplified and arguably unanswerable question.
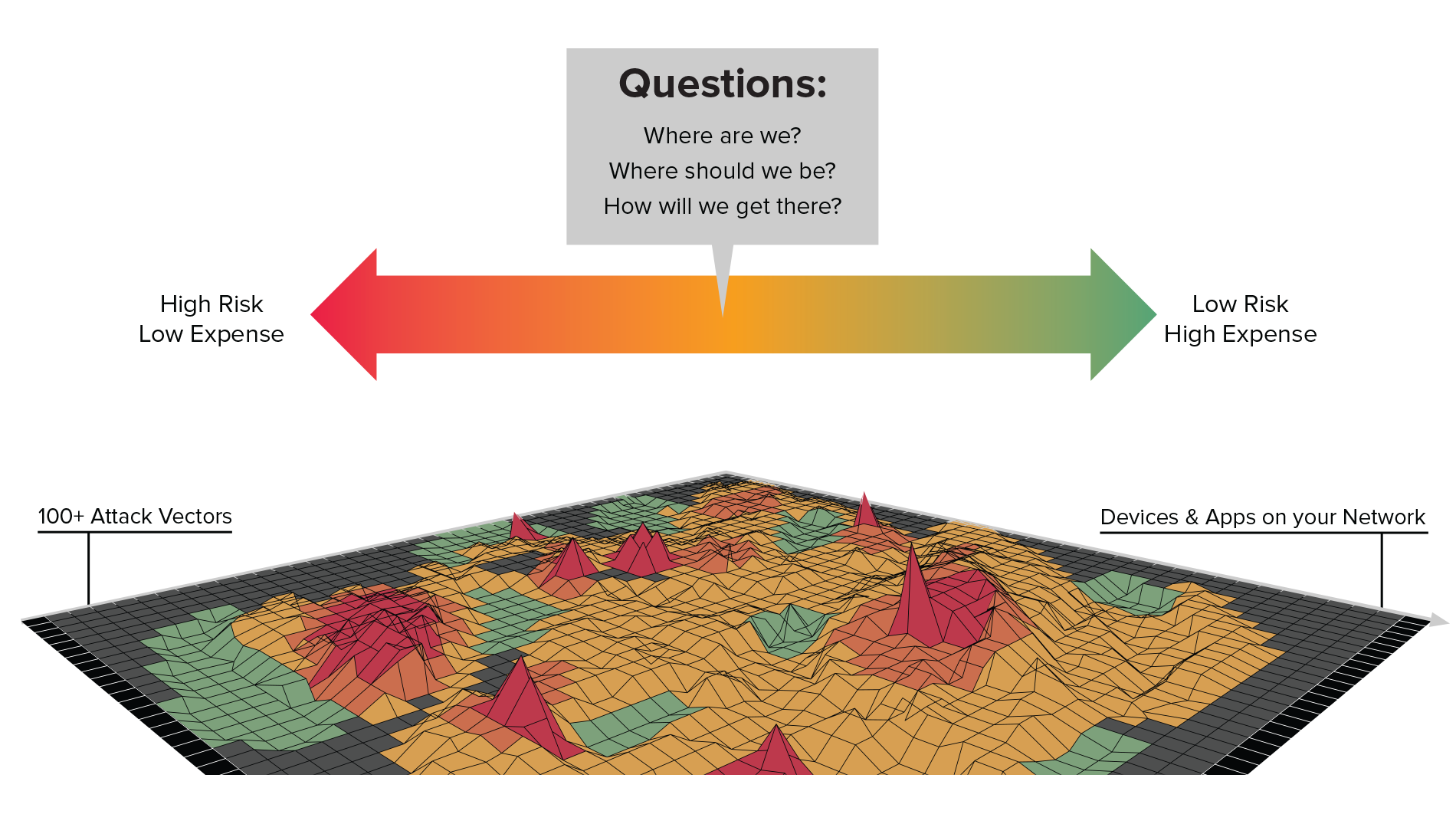
No enterprise is 100% secure and, given enough adversarial effort, any organization can be breached. Instead of discussing cybersecurity as a binary objective, CISOs and CIOs can help their board members think of cyber risk as a spectrum.
When considering this spectrum, there are three questions that your board has in mind. Your job is to help them answer:
- Where are we on the cyber-risk spectrum?
- Where do we want to be?
- How do we get there?
1. Where are we?
To get the conversation rolling, identify where your company is on the cyber risk spectrum. Quantify your views with risk scores based on your current security controls and the business impact of a breach. Benchmarking your cyber risk against similar organizations can also help to understand where you are.
Cybersecurity metrics are not tangible for non-technical stakeholders, so framing risk in terms of dollar impact to the business can be a good way to level the conversation. For more information on calculating and sharing your cyber risk levels, check out our eBook on Decoding Cyber Risk.
2. Where do we want to be?
An open conversation with the board and senior colleagues about where the organization should be on the cyber risk spectrum is key to getting alignment. If your company is like most, you’re on the yellow part of the spectrum quickly slipping into orange and red. Your attack surface is rapidly expanding as data grows and technology accelerates. In addition, your employees are likely shifting towards remote work, which brings a whole new layer of security concerns.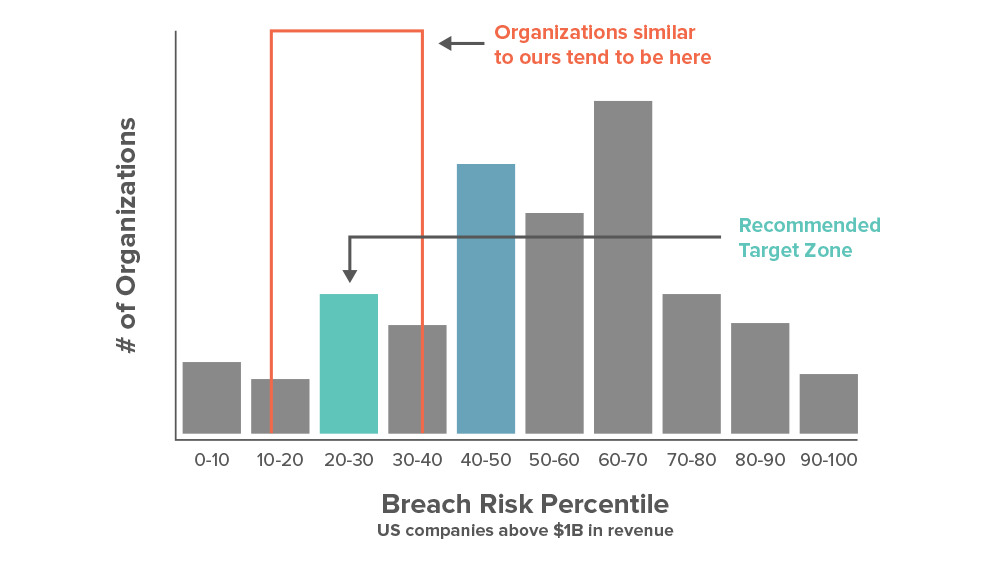
Depending on the type of customer data you store or sensitivity of IP you own, being in the yellow/orange risk area may or may not be acceptable. Share your thoughts on where you think the organization should be given the potential impact of a breach in dollars. Institutions like Equifax, large banks, and the Pentagon should invest in cybersecurity to the point where chances of a breach are almost non-existent. Most other organizations will have a risk appetite that falls somewhere in between light green and orange on the spectrum.
3. How do we get there?
The board has come to a consensus on the appropriate cyber risk level for your organization given the available budget and the criticality of a potential breach. Now they want to know: how do we get there?
In order to answer this question effectively, CISOs need to know the most vulnerable areas of their security posture. Cybersecurity technologies like Balbix have this intel available in real-time, with risk heat maps and prioritized risk insights.
Present the top three to five risk groups that need to be addressed to decrease cyber risk, detailing the likelihood of a breach and business impact of a breach for each area. Then, give a plan of attack for mitigating each, whether it be a software update project, an investment in a new tool, a training for certain risk owners, or something else.
Aligning the Business on Cybersecurity
Balbix was built to help CISOs and other cybersecurity leaders answer these questions accurately and effortlessly. Real-time, exportable risk dashboards and heat maps become the source of truth for many Balbix customers in their cybersecurity reporting. Google-like natural language search makes any cybersecurity question just a click away. Type in “where will the attack start?” and get a list of assets with the highest likelihood of being breached.
maps become the source of truth for many Balbix customers in their cybersecurity reporting. Google-like natural language search makes any cybersecurity question just a click away. Type in “where will the attack start?” and get a list of assets with the highest likelihood of being breached.
Reporting and quantifying cyber risk doesn’t have to be a pain. Read our Ultimate Guide to Cyber Risk Reporting to learn how you can leverage these conversations to further your cybersecurity goals or Schedule a Demo today to see how Balbix helps infosec leaders ace their board-level presentations.
