

December 9, 2021
Recently, Twitter user Sean Gallagher, Threat Researcher and former Cybersecurity Editor, posed this question to his 25K followers: what’s the dumbest security advice you’ve ever heard? At last check, his post had received over 400 replies ranging from funny to the obvious and everything in between. We have curated the most “liked” ones in this blog. Check out the entire thread.
Contributed by: Rob Graham (@ErrataRob)
Why is it dumb: If it looks sus, we definitely won’t trust it, duh! And BTW, the whole idea behind phishing emails is that they make them look legit to trick users!

Contributed by: Lesley Carhart (@hacks4pancakes)
Why is it dumb: Because this reeks of the security team’s inability to abstract the risk away from the users and then throwing their hands up in the air saying, “that’s all we can do!”
Contributed by: Adrian Sanabria (@sawaba)
Why is it dumb: Because it is TWO factor authentication, i.e you need to have two different factors (such as a password and a phone/email/biometric) to prove identity: something you know, something you have, something you are.
Contributed by: Michael Seirchio
Why is it dumb: It depends. It is a bad idea to create passwords based on a dictionary word and substituting some of the letters for numbers or symbols isn’t that clever as well. Password crackers know to include words like “vuln3rabl3” or “trustno1” in their lookup tables.
To be fair, using mixed case, numbers and special characters makes the password much stronger than just using lowercase. While exact figures will vary based on the amount of processing power on hand, a modern computer will take two days to crack an eight-character password, so your best bet is to have longer passwords.
Contributed by: Dimitry McKay (@dimitrimckay)
Why is it dumb: It’s obvious, right? No organization can characterize all assets as critical. Asset business criticality is determined by both its inherent properties like asset category (laptop, server, storage, etc.), business unit and geography and contextual properties like role of the asset, user privileges, and its interaction with other assets.

Contributed by: Spy604 (@spy604)
Why is it dumb: In organizations with no network segmentation, attackers can rapidly move laterally across the network from an initial compromised asset. Individual system compromises can easily turn into major data breaches.
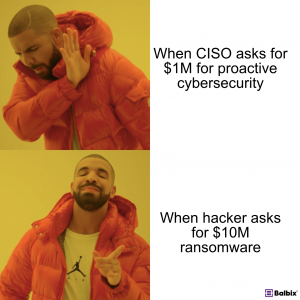
Contributed by: Z3ROTrust (@z3r0trust)
Why is it dumb: WELL? Because this is usually followed by “8 months later… “We had to pay $3 million in ransom to decrypt our files.”
Contributed by: Intruder (@IntruderVS1400)
Why is it dumb: While this is not necessarily dumb advice, it is hard to do due to long, unprioritized lists of vulnerabilities and resource-constrained teams. Organizations need to prioritize vulnerabilities and patch in order of importance.
Comment on our LinkedIn post and tell us the dumbest security advice that you’ve ever heard.