
November 20, 2023
This month, Microsoft announced fixes for 58 new vulnerabilities this month, including 3 new zero-day vulnerabilities, 1 updated to a previously identified zero-day and 3 Microsoft-rated critical vulnerabilities. This month there were 3 new zero-day vulnerabilities disclosed (as well as an update to 1 previously disclosed zero day from September 2023). Also, there were updates to 9 previously reported CVE’s and 1 previously released advisories (see the full list on the Microsoft Security Response Center (MSRC)
Of the 58 new vulnerabilities, the fix sources breakdown as follows:
This month’s headline continues to be the release of zero-day vulnerabilities of where there were three new zero-days this month (CVE-2023-36025, CVE-2023-36033, CVE-2023-36036).
The first of these vulnerabilities, CVE-2023-36025, while the exploit has not be publicly disclosed, has the potential to bypass the smart screen authentication feature if turned on.
The second zero-day vulnerability (CVE-2023-36033), this one with a publicly disclosed exploit, impacts the Desktop Window Manager (DWM) which is responsible for the desktop composition experience. Through desktop composition, DWM enables visual effects on the desktop as well as various features such as glass window frames, 3-D window transition animations, Windows Flip and Windows Flip3D, and high resolution support. Due to this universal presence on every windows system and the fact that an exploit has been released which allows for the elevation of privilege by the attacker, this is particularly noteworthy.
Finally the third zero-day vulnerability (CVE-2023-36036) affects Windows Cloud Files Mini Filter Driver which is one of the components responsible for managing interaction with file systems, the details of which are beyond the scope of this note. (see: Learn About Filter Manager Concepts on Microsoft Docs). The vulnerability, if exploited would allow for SYSTEM access to the operating system.
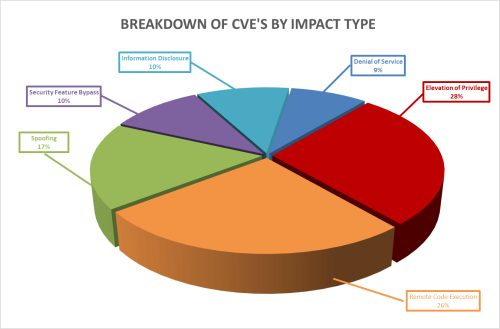
Breaking down the complete set of 58 vulnerabilities further by impact type, we can see that Elevation of Privilege leads the way this month, with Remote Code Execution closely following behind it.
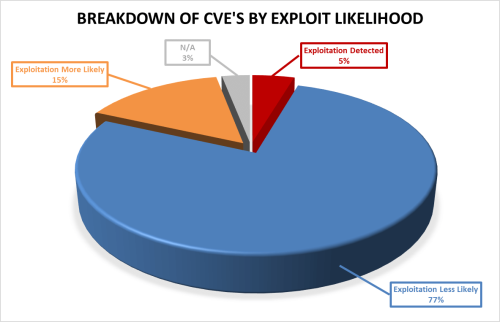
Furthermore, as seen below, these vulnerabilities vary in how likely they are to be exploited, with 20% of the vulnerabilities this month either already exploited or highly likely to be exploited, as ranked by the Microsoft Exploitability Index.
As always, Balbix can identify all affected assets within hours of release. There are no scans to run. Balbix customers simply search for the CVE name in their Balbix dashboard to view the list of affected assets. Filtered search functionality can also be used to search for the CVE by site, subnet, location, or other distinguishing factors.