
November 9, 2022
Well daylight savings time for much of the United States has arrived. Changing clocks is always a good reminder to do other maintenance like change your smoke alarm batteries, put in new air filters in your house, and yes, clean up your cybersecurity environment.
It is the last of these that is the subject of this blog. Microsoft has released its November “Patch Tuesday” fixes. This month Microsoft announced patches for 62 threats, including 10 deemed critical and four zero-days. The headline issues this month are:
CVE-2022-37966 – Windows Kerberos RC4-HMAC Elevation of Privilege Vulnerability
CVE-2022-41091– Windows Mark of the Web Security Feature Bypass Vulnerability
These two vulnerabilities are featured for very different reasons.
CVE-2022-37966 is a vulnerability in the core security protocol (Kerberos) within the Microsoft ecosystem. It is a low complexity attack that can be carried out by anyone with network access.
CVE-2022-41091 represents a bypass of the important Mark of the Web (MotW) protection provided to users when downloading files from untrusted sources.
Microsoft also released updates to 16 existing CVEs.
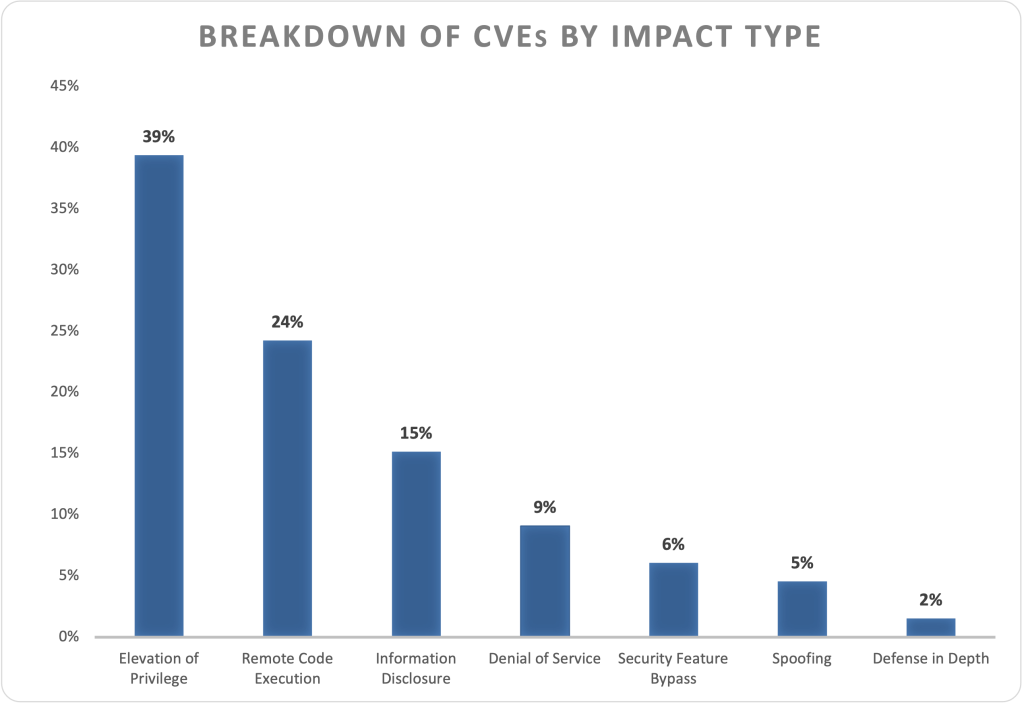
Breaking down the fixes further, we can see that elevation of privileges and remote code executions lead the way this month.
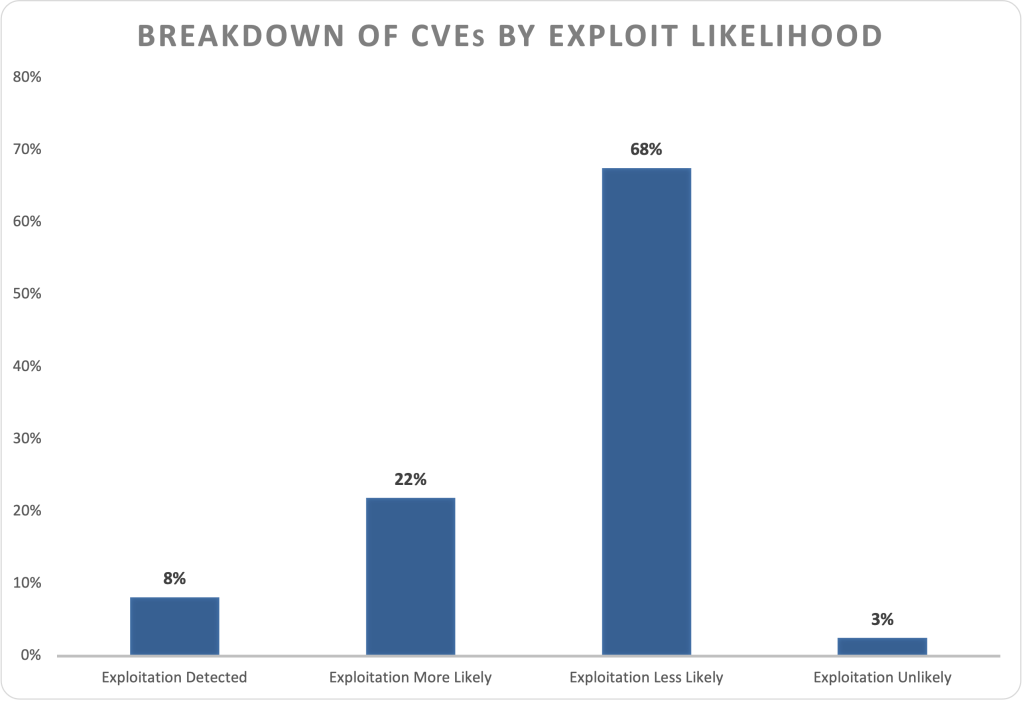
These vulnerabilities vary in terms of how likely they are to be exploited, with 30% of this month’s vulnerabilities either already exploited or highly likely to be exploited.
As always, Balbix can identify all affected assets within 1 hour of release. There are no scans to run. Balbix customers simply search for the CVE name in their Balbix dashboard to view the list of affected assets. Users can also use the filtered search functionality to search for the CVE by site, subnet, location, or other distinguishing factors.