
April 12, 2023
April showers bring … well, more new patch fixes from Microsoft. I don’t think that’s how the saying goes but here we are, nonetheless. This month, Microsoft announced patches for 97 new vulnerabilities, including 7 that Microsoft has rated critical, and 1 zero-day (CVE-2023-28252). This release also included updates to 5 previously released CVE’s (one of which is known exploitable – CVE-2013-3900).
Of the 97 new vulnerabilities, 78 have Knowledgebase (KB) fixes, 14 have release notes associated with them, 1 click-to-run update, 2 updates from the Microsoft App Store, and 2 downloadable product security updates.
The headline issue this month is the one known exploitable zero-day CVE:
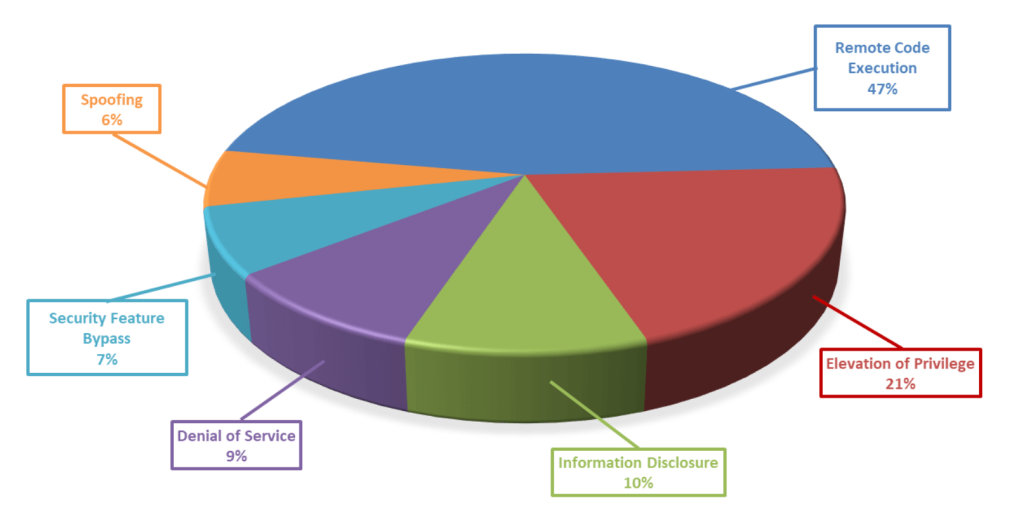
Breaking down the 97 vulnerabilities further, we can see that remote code execution and elevation of privileges continue leading the way again this month, and for the year, in terms of impact type.
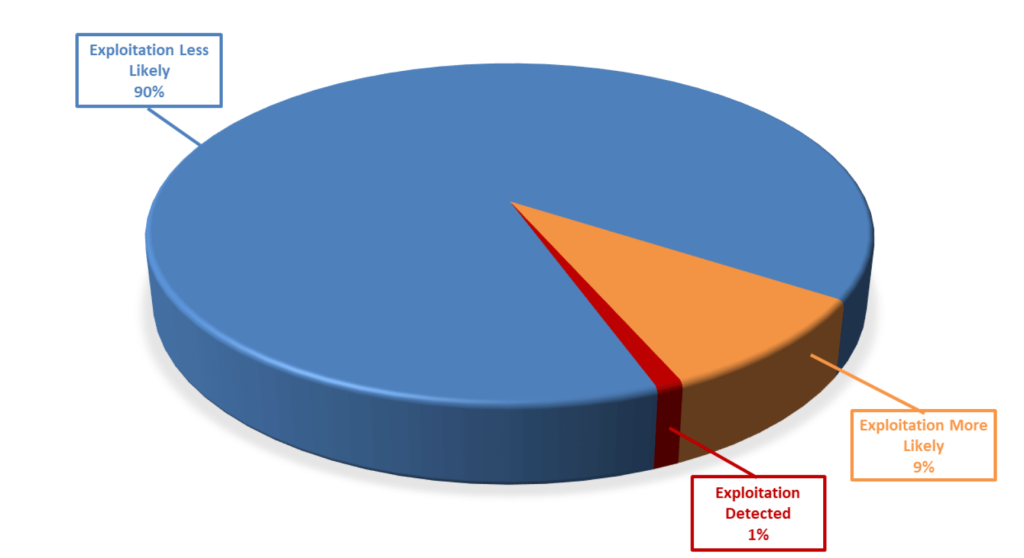
Furthermore, as can be seen below, these vulnerabilities vary in terms of how likely they are to be exploited, with 10% of the vulnerabilities this month either already exploited or highly likely to be exploited.
As always, Balbix can identify all affected assets within hours of release. There are no scans to run. Balbix customers simply search for the CVE name in their Balbix dashboard to view the list of affected assets. Filtered search functionality can also be used to search for the CVE by site, subnet, location, or other distinguishing factors.
If you have additional questions, please contact support@balbix.com.